John Daghita aka “John/Lick” Arrested in Alleged Cryptocurrency Theft Tied to US Marshals Service

Key takeaways
- In October 2024, more than USD 20 million in cryptocurrency was stolen from a wallet controlled by the U.S. government. While the majority of the funds were returned following outreach from the FBI, a portion of the stolen assets was not recovered.
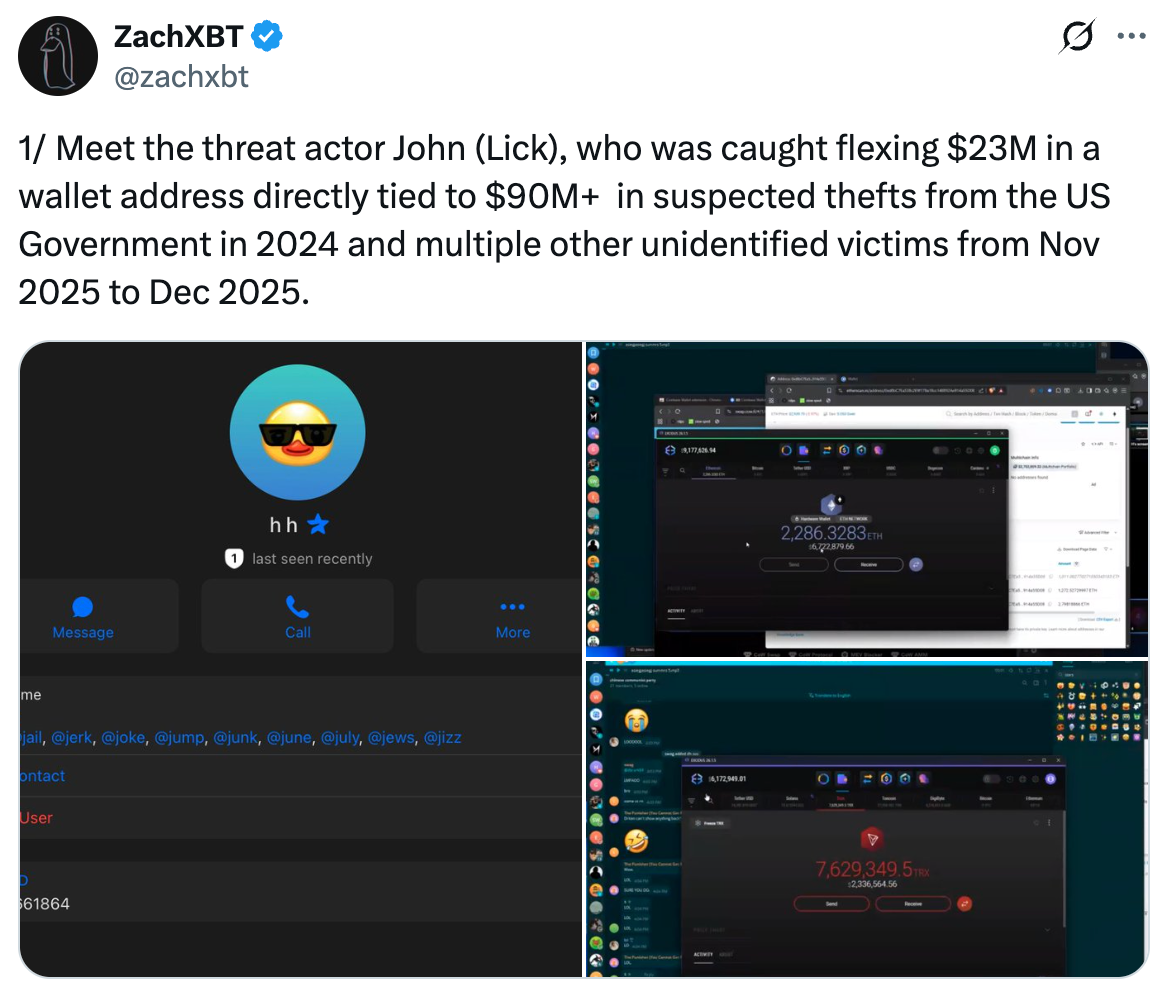
- In January 2026, during an online “band-for-band” exchange — a social media trend in which participants publicly display and compare their crypto holdings — blockchain investigator ZachXBT observed a participant using the handle “John” or “Lick” moving funds linked to the earlier theft from the government wallet.
- After the activity was publicly attributed to him, the actor behind the “John/Lick” persona began moving funds through mixers and across blockchains in an apparent effort to obscure the origin and ownership of the stolen assets.
- Yesterday, John Daghita was arrested on the Caribbean island of Saint Martin. The arrest appears consistent with ZachXBT’s earlier assessment linking Daghita to the “John/Lick” wallets involved in the movement of the stolen funds.
{{horizontal-line}}
John Daghita, accused of stealing tens of millions of dollars in cryptocurrency from wallets associated with the US Marshals Service, was arrested on the Caribbean island of Saint Martin in a joint operation conducted by the French Gendarmerie and the Federal Bureau of Investigation. The arrest was publicly confirmed by FBI Director Kash Patel, who announced the development on his official X account and released images from the operation showing seized hardware wallets and a briefcase containing US currency.

The case represents one of the most unusual cryptocurrency theft investigations in recent years. It involves an individual allegedly connected to a firm responsible for safeguarding seized digital assets on behalf of the United States government and highlights how blockchain transparency, open-source investigation, and law enforcement collaboration can unravel even sophisticated attempts to conceal stolen cryptocurrency.
TRM Labs is proud to support the US government in its ongoing investigation into this theft. The case was led by the FBI’s Washington Field Office, with support from cryptocurrency investigative specialists based in the FBI’s Cleveland Field Office.
The origins of the investigation
The case first gained public attention in January 2026 when blockchain investigator and TRM partner ZachXBT disclosed findings linking a pseudonymous cryptocurrency user known online as “John” or “Lick” to a network of wallets controlling large quantities of suspected illicit funds.
According to ZachXBT’s analysis, the wallets appeared to control more than USD 90 million in cryptocurrency associated with suspicious activity, including funds traced to wallets controlled by the US government. Approximately USD 24.9 million of the traced funds originated from a US government-controlled wallet containing cryptocurrency seized in connection with the 2016 Bitfinex hack.
Those seized assets were part of the pool of cryptocurrency that could ultimately contribute to the US Strategic Bitcoin Reserve referenced in the March 2025 Executive Order on Digital Assets.
During the investigation, ZachXBT also noted rumors circulating within cryptocurrency communities suggesting that the individual controlling the wallets might be John Daghita, the son of Dean Daghita, president of Command Services & Support (CMDSS). CMDSS is a Virginia-based company that received a contract from the US Marshals Service in October 2024 to assist with the custody and disposition of certain categories of seized cryptocurrency.
At the time of ZachXBT’s disclosure, authorities had not made any allegations regarding Daghita’s involvement. However, the subsequent arrest of John Daghita appears to support the attribution linking him to the wallets under investigation.
The Telegram “band-for-band” exchange
The investigation itself began with an unusual moment of public exposure.
On January 23, 2025, participants in a private Telegram group engaged in what is commonly referred to in cryptocurrency communities as a “band-for-band” exchange. In these exchanges, participants attempt to demonstrate their wealth by showing wallet balances or moving cryptocurrency in real time.
During the exchange, the user known as “Lick” screen-shared an Exodus wallet displaying a TRON address holding approximately USD 2.3 million. Over the course of the conversation, additional transactions were broadcast live, including a transfer of roughly USD 6.7 million worth of ether into an Ethereum address controlled by the same participant.
By the end of the exchange, approximately USD 23 million had been consolidated into a single wallet.
Because the transactions occurred live and were accompanied by screen-sharing, ZachXBT was able to directly observe wallet addresses, transaction hashes, and consolidation behavior. This real-time visibility provided unusually strong attribution evidence linking the Telegram user to the wallets involved.
Tracing the Funds from Government-Controlled Wallets, Through Mixers, To Landing Spots
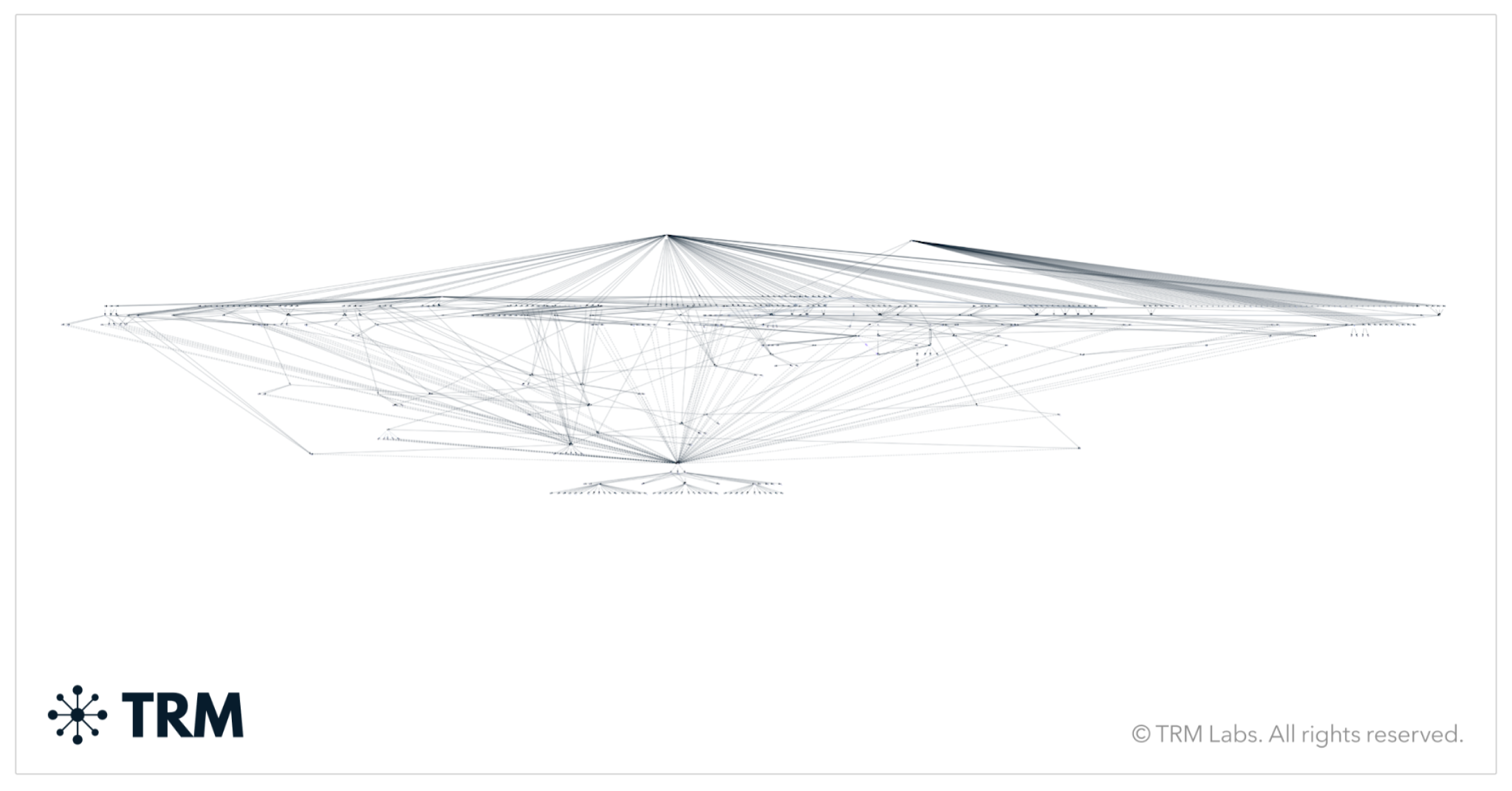
After identifying the wallets involved in the Telegram exchange, ZachXBT traced the transaction history backward across the blockchain and made the connection to the March 2024 theft from the US Government wallet.
Shortly after ZachXBT’s reporting, the funds began to move across blockchains, through mixers, and into other on-chain obfuscation mechanisms. Alerted to the online expose, the FBI was able to track the funds through the laundering mechanisms and identify ‘de-mixed’ consolidation addresses and potential cash-out points.
Arrest in Saint Martin
The investigation ultimately culminated in the arrest of John Daghita on the Caribbean island of Saint Martin.
French Gendarmerie tactical units carried out the arrest in coordination with the FBI, reflecting the increasingly international nature of cryptocurrency investigations. Criminal actors may move digital assets across borders instantly, but law enforcement cooperation across jurisdictions has grown alongside the technology.
Images released following the arrest show investigators recovering a briefcase containing US currency as well as several hardware cryptocurrency wallets.
Hardware wallets are frequently used to store significant amounts of cryptocurrency offline and can serve as critical pieces of evidence linking suspects to specific blockchain addresses.
Blockchain evidence and asset recovery
The case illustrates a fundamental reality of cryptocurrency investigations: although actors may attempt to conceal illicit proceeds through mixers, cross-chain transfers, or complex transaction chains, the underlying blockchain records remain permanently visible.
Ali Comolli, TRM Labs Global Capacity Building Lead and a former FBI analyst turned federal prosecutor, emphasized this point. “In crypto, blockchains don’t forget and neither does the U.S. Government. The FBI is exceptionally capable at tracing cryptocurrency, and I expect we’ll see forfeiture initiated as soon as possible to return these stolen funds to their rightful owners.”
Law enforcement agencies increasingly rely on blockchain intelligence to trace stolen cryptocurrency across exchanges, mixers, and cross-chain bridges. These capabilities have enabled investigators to recover funds in cases ranging from ransomware attacks to major exchange hacks.
Public-private collaboration in crypto investigations
The investigation also underscores the growing importance of collaboration between law enforcement agencies, independent blockchain investigators, and analytics platforms.
TRM Labs works closely with government agencies and investigative partners to provide blockchain intelligence that supports attribution, transaction tracing, and the disruption of illicit financial activity across the digital asset ecosystem.
Through initiatives such as the TRM Beacon Network, investigators and virtual asset service providers can collaborate in near real time to identify suspicious wallet addresses and prevent illicit funds from being cashed out through exchanges.
This model reflects a broader shift in financial crime investigations. Rather than relying solely on retrospective analysis, investigators can now identify and disrupt illicit financial flows while transactions are still unfolding.
The investigation continues
While the arrest represents a major development, the case remains ongoing.
Authorities are expected to pursue forfeiture proceedings aimed at recovering any remaining stolen assets and returning them to US government custody. Investigators will also continue tracing funds that may have moved through exchanges, bridges, and mixers following the initial theft.
The case highlights a recurring lesson in blockchain investigations: even sophisticated attempts to conceal illicit cryptocurrency can unravel through operational mistakes, public exposure, or overconfidence.
Immutable blockchain records allow investigators to reconstruct financial activity across chains, exchanges, and wallets long after actors believe their tracks have been erased.
TRM Labs will continue to monitor the case as it develops.
{{horizontal-line}}
Frequently Asked Questions (FAQs)
1. Who is John Daghita and why was he arrested?
John Daghita was arrested on the Caribbean island of Saint Martin in a joint operation involving the French Gendarmerie and the FBI. Authorities allege that he was involved in the theft of cryptocurrency from wallets associated with the US Marshals Service. The arrest appears consistent with earlier blockchain analysis, conducted by crypto investigator ZachXBT, that linked Daghita to the online personas “John” or “Lick,” which were associated with wallets moving funds connected to the theft.
2. How were investigators able to identify the wallets linked to the theft?
Blockchain investigator ZachXBT observed suspicious transactions during a Telegram “band-for-band” exchange — a social media trend where participants display their crypto holdings. During the exchange, a participant using the name “Lick” publicly screen-shared wallet balances and transactions. Because these transactions occurred live, the investigator was able to capture wallet addresses and trace their transaction history on-chain, eventually linking the funds back to a government-controlled wallet.
3. What cryptocurrency was stolen from the US government wallet?
The stolen assets were linked to cryptocurrency previously seized by US authorities in connection with the 2016 Bitfinex hack. Approximately USD 25 million of those seized assets were reportedly moved during the theft incident in 2024. While a significant portion of the funds was later returned following FBI outreach, some assets remain unrecovered.
4. Why were the stolen funds difficult to trace?
After the wallets were publicly identified, the actor controlling the funds began moving assets across blockchains and through cryptocurrency mixers — services designed to obscure transaction histories. Despite these attempts, investigators were able to continue tracing the funds because blockchain transactions remain permanently recorded and can often be reconstructed through advanced blockchain intelligence techniques.
5. What does this case show about cryptocurrency investigations?
The case highlights how blockchain transparency, open-source intelligence, and cooperation between investigators can play a critical role in identifying illicit activity. Even when actors attempt to hide funds through mixers or cross-chain transfers, the underlying blockchain records remain accessible for analysis, allowing investigators to reconstruct transaction flows over time.





















