North Korean Hackers Attack Drift Protocol In USD 285 Million Heist

Key takeaways
- On April 1, 2026, attackers drained approximately USD 285 million in user assets from Drift Protocol — the largest decentralized perpetual futures exchange on Solana — in roughly 12 minutes, with most stolen funds bridged to Ethereum within hours.
- On-chain staging began on March 11, nearly three weeks before the April 1 execution — with attacker infrastructure, token manufacturing, and social engineering all running in parallel with careful coordination.
- The critical vulnerability was not a smart contract bug but a combination of social engineering multisig signers into pre-signing hidden authorizations and a zero-timelock Security Council migration that eliminated the protocol's last line of defense.
- The attacker manufactured an entirely fictitious asset — CarbonVote Token — with a few thousand dollars in seeded liquidity and wash trading, and Drift's oracles treated it as legitimate collateral worth hundreds of millions of dollars.
{{horizontal-line}}
On April 2, 2026, Drift Protocol confirmed that attackers drained approximately USD 285 million in user assets on April 1, 2026. This is the largest DeFi hack of 2026 — and the second-largest exploit in Solana's history, behind only the USD 326 million Wormhole bridge hack in 2022. TRM’s initial investigation suggests the hack was likely perpetrated by North Korean hackers.
What is Drift, and how exactly did this happen?
Drift is the largest decentralized perpetual futures exchange on the Solana blockchain, allowing users to trade leveraged positions without a centralized intermediary. It held billions in user assets, which made it a high-value, high-complexity target.
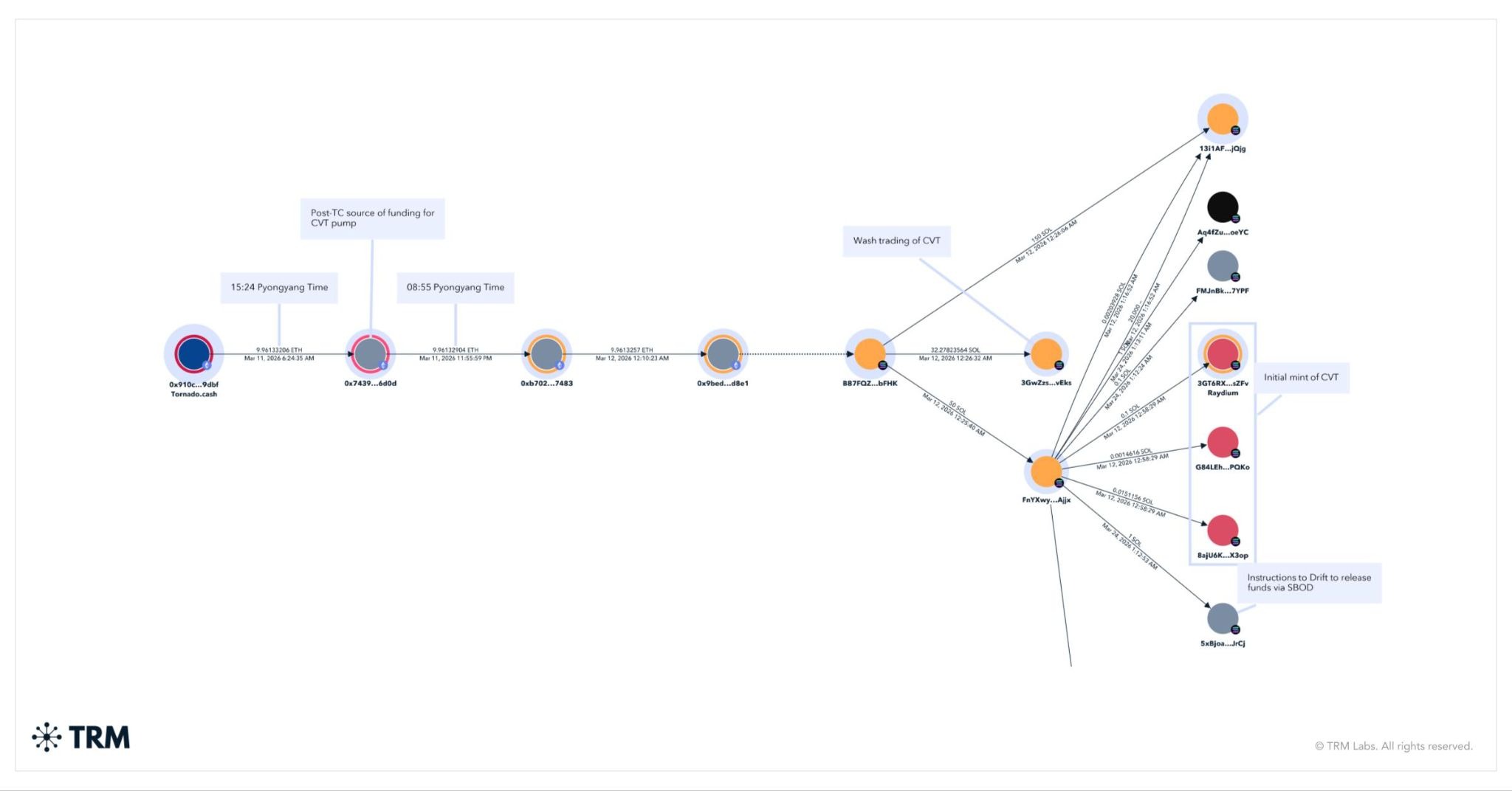
The attack did not begin on April 1. On-chain staging began weeks earlier, on March 11th, with a single withdrawal of 10 ETH from Tornado Cash. These ETH began moving hours later at around 12:00 AM GMT on March 12th — or around 09:00 Pyongyang time — and shortly after funded the deployment of CarbonVote (CVT), the token used to manipulate Drift.
Between March 23 and March 30, the attacker created multiple "durable nonce" accounts — a legitimate Solana feature that allows transactions to be pre-signed and executed later without expiring. The attacker used social engineering to induce Drift Security Council multisig signers into pre-signing transactions that appeared routine but carried hidden authorizations for critical admin actions.
On March 27, Drift migrated its Security Council to a new 2/5 threshold configuration with zero timelock — eliminating the delay that would have allowed detection and intervention. That migration created the exploitable gap.
In parallel, the attacker spent weeks manufacturing legitimacy for a fake token — CarbonVote Token (CVT) — minting 750 million units, seeding just a few thousand dollars in liquidity on Raydium, and using wash trading to build a price history near USD 1. Drift's oracles picked up that artificial signal and treated CVT as a real asset.
On April 1, those pre-signed transactions were deployed. The attacker listed CVT as valid collateral on Drift, raised withdrawal limits to extreme levels, and deposited hundreds of millions in CVT against that manufactured price. Then 31 withdrawal transactions executed in roughly 12 minutes — draining real assets including USDC and JLP from the protocol.
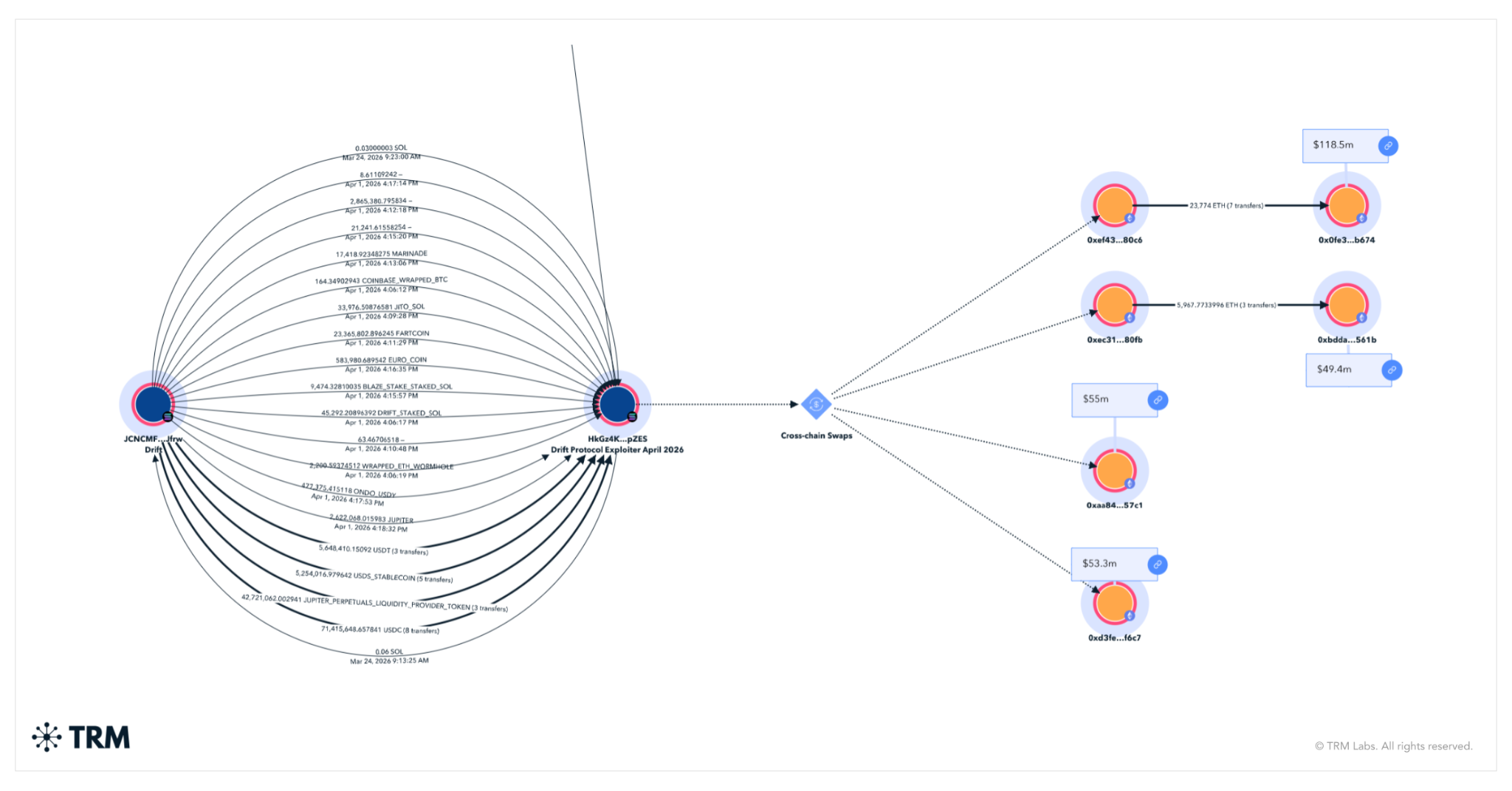
Drift suspended deposits and withdrawals. The DRIFT token fell over 40%. Most of the stolen funds were bridged within hours to Ethereum.
The confidence of the hackers was staggering. Each bridging transaction moved hundreds of thousands or, more often, millions in USDC, far outstripping the speed and aggressiveness of even the Bybit laundering of 2025.
TRM Labs, which was the first blockchain intelligence company to cover Solana, and has the most complete coverage of the blockchain today, is actively tracking the cross-chain funds movement and monitoring on-chain indicators related to potential state actor involvement. More to come as the picture develops.
{{horizontal-line}}
Frequently asked questions
1. What happened to Drift Protocol?
On April 1, 2026, attackers drained approximately USD 285 million in user assets from Drift Protocol, the largest decentralized perpetual futures exchange on Solana.
3. How does this compare to other major hacks?
At USD 285 million, the Drift exploit is the largest DeFi hack of 2026 and the second-largest in Solana's history, behind only the USD 326 million Wormhole bridge hack in 2022.
4. What should DeFi protocols do differently in light of this attack?
Three lessons are immediately apparent. First, timelocks on governance and admin actions are a critical safeguard — their removal, as happened here on March 27, eliminates the detection window that makes intervention possible. Second, oracle design requires defense-in-depth: protocols should require minimum liquidity thresholds, time-weighted price validation, and circuit breakers before accepting any asset as collateral. Third, multisig hygiene matters — signers should have robust processes for independently verifying the full content of any transaction before signing, particularly those touching admin functions.





















