Cross-chain Swap Traceability: Seven Models, One Engineering Framework

Every week, billions of dollars move between blockchains — Bitcoin to Solana, ETH to TRON, USDC from Ethereum to Base. Most of that movement is invisible to the tools that are supposed to track it.
Cross-chain swaps (CCS) are the infrastructure making multi-chain crypto usable. But "cross-chain swap" is not one thing. It's a family of mechanisms — bridges, liquidity protocols, centralized swap desks, custodial ledgers — each making different trade-offs around speed, trust, and transparency. And each putting the "truth" of the transaction somewhere different: sometimes in an on-chain message, sometimes in an internal ledger, sometimes nowhere you can directly observe.
At TRM, we've built analytics coverage across the full spectrum of these models. This post breaks down what we found: how each mechanism actually works, what it exposes to an analyst, and where the hard problems live. By the end of this post, you'll have a working mental model of the major cross-chain swap (CCS) mechanisms, understand where "'truth"' lives in each, and know what it takes to build traceable analytics across all of them.
{{horizontal-line}}
Key takeaways
- A cross chain swap (CCS) isn’t one thing: it’s multiple linkage models with different “truth locations” (where the swap can be proven).
- Traceability is a design choice: it depends on whether intent is on-chain, liquidity is fronted, or inventory/ledger is internal.
- The hard part isn’t detecting deposits and withdrawals — it’s linking them with quantified confidence.
- Risk concentrates in (a) contract compromise, (b) validator/relayer compromise, (c) liquidity insolvency, and (d) custody opacity.
- If you want scalable analytics, you need a canonical cross-chain swap event schema — not one-off heuristics.
{{horizontal-line}}
How value actually moves across blockchains — and why it matters more than ever
What happens when you want to trade your Bitcoin (BTC) for Solana (SOL)?
You don’t think about blockchains. You think about outcomes. You have Bitcoin. You want SOL. Or USDC on Base. Or ETH on Arbitrum. Or USDT on TRON.
But under the hood, those assets live on different networks with different rules, validators, and consensus systems. There is no built-in “send across chains” button in crypto.
So how does value move from one blockchain to another?
The answer is cross-chain swaps (CCS) — the invisible infrastructure that makes multi-chain crypto usable.
In 2026, CCS isn’t a niche technical feature. It’s the connective tissue of a fragmented blockchain world. But not all CCS systems are created equal — and the way they’re designed fundamentally changes:
- UX and fulfillment speed
- Liquidity efficiency
- Decentralization and trust assumptions
- Exploit and insolvency risk
- Traceability and observability
{{horizontal-line}}
What are cross-chain swaps?
A cross-chain swap (CCS) is a mechanism that allows a user to move value from one blockchain (or asset domain) to another.
Historically, this was mostly done through bridges:
- Lock tokens on chain A
- Mint or release equivalent tokens on chain B
- Reverse the process when exiting
In 2026, CCS haves evolved into a diverse ecosystem of models that solve the “same” problem in radically different ways.
The critical question behind every CCS system is:
Who fronts liquidity, who assumes risk, and where does the truth of the transaction live?
{{horizontal-line}}
Definitions and contracts
CCS discussions get muddy fast because the same word describes very different things. Here’s the minimum vocabulary to keep the rest of this post crisp.
“Swap” vs “movement”
- A swap is the user’s intent: “I want asset X on chain A → asset Y on chain B.”
- A movement is what shows up in data: deposits, burns, mints, transfers, withdrawals.
Many CCS systems do not produce a single “swap transaction.” They produce a bundle of movements across chains plus off-chain coordination.
Fulfillment vs. settlement
Some systems fulfill immediately (user receives funds quickly) but settle later (LPs, solvers, or protocols reconcile accounting after the fact).
- Fulfillment: User gets the destination asset
- Settlement: The system makes LPs/protocol whole, proves messages, finalizes reconciliation
This distinction matters because fulfillment can be visible even when settlement is delayed or opaque.
Truth location
“Where the swap can be proven” differs by model:
- Source-chain truth (locks/burns with canonical identifiers)
- Destination-chain truth (mints/releases with message proofs)
- Messaging-layer truth (cross-chain message ID / proof system)
- Inventory truth (internal hot wallets / treasury movements)
- Ledger truth (exchange books / custodial internal accounting)
{{horizontal-line}}
Linkage types
{{horizontal-line}}
System overview: The CCS pipeline (one mental model)
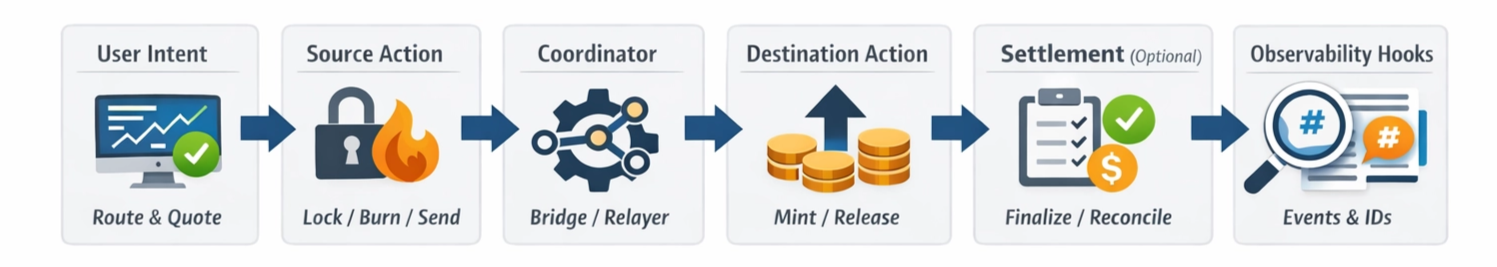
Even though CCS models vary, most swaps follow a common shape:
- User intent (route selection / quote / UI)
- Source action (lock, burn, send to router, deposit to service)
- Coordinator (bridge contract, relayers, solvers, centralized service)
- Destination action (mint, release, LP transfer, exchange withdrawal)
- Settlement (optional; reimbursement, message finality, reconciliation)
- Observability hooks (events, message IDs, deposit addresses, memos)
Every CCS model is just a different instantiation of this pipeline.
{{horizontal-line}}
Worked examples: The same user outcome, radically different “truth”
To see why CCS traceability varies so much, it helps to walk through an end-to-end swap in two different models.
Example A: BTC → SOL via a traditional bridge
Happy path
- The user initiates a bridge transfer of a BTC representation to Solana (e.g. an EVM → Solana transfer tracked by WormholeScan).
- On the source chain, the bridge emits a message that encodes the intent: “lock/burn X; redeem/mint on Solana.”
- That message is assigned a stable identifier (Wormhole VAAs are uniquely identified by
(emitter_chain, emitter_address, sequence)). - On Solana, the Token Bridge program verifies the proof/message and executes the redeem, minting/releasing the corresponding token on Solana.
- The user now holds bridged BTC on Solana (commonly Portal wBTC mint:
3NZ9JMVBmGAqocybic2c7LQCJScmgsAZ6vQqTDzcqmJh). - (Optional) The user swaps that bridged BTC for SOL on a Solana DEX.
What’s observable (and why it’s strong)
- A source transaction that produced the bridge message
- A message identifier (VAA key: emitter chain/address + sequence) — the linkage key
- A destination redeem transaction on Solana that consumes that exact message/proof
- The resulting token state on Solana (e.g. the bridged BTC mint shown above)
Linkage type: Deterministic
Because the destination redeem is cryptographically tied to a specific source-emitted message/proof, the source → destination mapping is provable (best case).
Where it breaks down in practice
- Wrapped asset lifecycle: Representation mints/burns can confuse “net flow” if you’re treating wrapped tokens like native BTC.
- Batching/aggregation: Multiple source-side actions may settle into fewer destination actions (or vice versa).
- Upgrades/migrations: Contract/program upgrades can change event shapes and break older parsers — even if the protocol still works.
Example B: BTC → SOL via a centralized instant swap service
Happy path
- The service gives the user a BTC deposit address (sometimes with a memo/tag).
- The user sends BTC to that deposit address.
- The service sends SOL from its inventory (typically a hot wallet) to the user’s Solana address.
- Internally, the service may hedge, rebalance, or net flows later — none of which needs to appear on-chain.
What’s observable (and what’s missing)
- A BTC deposit transaction into a service-controlled address
- A SOL withdrawal transaction from a service-controlled hot wallet to the user
- No on-chain message/proof that binds “this BTC deposit” to “that SOL payout”
Linkage type: Probabilistic
You can often see both legs clearly (deposit + payout), but the causal join — the “truth” — lives inside the service’s internal ledger. On-chain, you infer linkage using timing, amounts, and behavioral patterns rather than a shared identifier.
Where it breaks down in practice
- Pooled hot wallets: Many payouts originate from the same withdrawal wallet(s).
- Batched withdrawals: One transaction pays many recipients, weakening pairwise linkage.
- Variable spreads/fees: The SOL payout may not be a clean function of the BTC deposit amount.
- Internal netting: Deposits don’t necessarily trigger immediate outbound transactions (payouts can be pre-funded or delayed).
{{horizontal-line}}
Models of cross-chain swaps in 2026

Below is a compact taxonomy of how CCS is implemented in practice (and what that implies for both users and analysts).
{{horizontal-line}}
Model deep dives
Below, each model is broken into:
- Happy path sequence
- What you can observe
- How linkage works
- Failure modes and edge cases
- What a robust analytics system needs
1. Traditional bridges (lock-and-mint / burn-and-mint)
Happy path
- User locks/burns on source chain
- Bridge emits an event (deposit / burn)
- Relayers/validators observe the event and submit an attestation/proof
- Destination contract verifies proof
- Destination contract mints/releases representation
- Exit reverses: Burn representation → unlock original
What you can observe
- Source: Lock/burn event, depositor, amount, token, destination parameters
- Messaging: Nonce / sequence / message hash (varies by protocol)
- Destination: Mint/release event tied to message proof
Linkage
- Deterministic if there’s a stable message identifier exposed in both domains
- Semi-deterministic if linkage requires protocol-specific decoding (e.g., nested logs, program traces)
Failure modes and edge cases
- Contract compromise (bridge exploit, mint-without-lock)
- Message replay / duplicate delivery (idempotency bugs)
- Finality mismatch (source tx appears then reorgs)
- Wrapped asset confusion (representation hops across venues before redemption)
- Rate-limits / pause switches (fulfillment stops mid-flight)
What analytics needs
- Protocol-aware event decoding
- Chain-specific finality + reorg handling
- Canonical “source action” ↔ “destination action” mapping
- Support for migrations / versioning across upgrades
2. DeFi liquidity bridges and cross-chain DEXs (LP-fronted)
Happy path
- User submits source chain action (deposit to router / bridge contract)
- Protocol quotes route + fee; may encode destination parameters
- LPs/solvers front liquidity on destination chain (fulfillment)
- Protocol later settles LPs (settlement) via proofs, reimbursements, or netting
What you can observe
- Source: Deposit/intent event, often with destination address
- Destination: LP payout transfer(s)
- Settlement: Reimbursements, message validation, or delayed accounting moves
Linkage
- Semi-deterministic when protocol exposes identifiers and structured flows
- Can degrade to probabilistic when:
- Payouts are batched
- Settlement is delayed or netted
- Multiple fills occur
Failure modes and edge cases
- Liquidity exhaustion (fulfillment fails or partial fills)
- Partial fills (multiple destination txs correspond to one source)
- MEV / routing variability (different solvers choose different execution paths)
- Fee-on-transfer / rebasing tokens (amount drift)
- Settlement delays (long gap between user payout and LP reimbursement)
What analytics needs
- Separation of fulfillment vs. settlement legs
- Confidence scoring (not just binary linkage)
- Protocol-specific batching detection
- Heuristics for partial fills + multi-output transfers
3. Centralized instant swap services (inventory-based)
Happy path
- Service issues deposit address / memo
- User deposits asset
- Service pays out destination asset from inventory
- Service rebalances later
What you can observe
- Deposit into service-controlled addresses
- Withdrawals from service-controlled inventory wallets
- Sometimes: memo/tag use (especially in account-based systems)
Linkage
- Often probabilistic:
- Time-window matching
- Amount matching (with spreads/fees)
- Behavior-based matching (known service patterns)
Failure modes and edge cases
- Batched withdrawals
- Pooled wallets shared across many services
- Intermediated routing (service uses a bridge/DEX behind the scenes)
- Internal netting (no immediate on-chain correlate)
What analytics needs
- Service entity resolution (cluster wallets + infra)
- Probabilistic linkage with explainability (“why we think these connect”)
- Detection of “service used a bridge behind the scenes” (multi-hop CCS)
4. Custodial exchange swaps (internal ledger)
Happy path
- User deposits asset to exchange
- Swap occurs off-chain in exchange ledger
- User withdraws destination asset to a blockchain address
What you can observe
- On-chain deposits and withdrawals
- (Often) deposit address mapping per user or per session (varies by exchange)
Linkage
- On-chain linkage is weak without cooperation
- Best you can often do is:
- Deposit attribution
- Withdrawal attribution
- Probabilistic connections when deposit/withdrawal are close and amounts align
Failure modes and edge cases
- Off-chain netting means no 1:1 mapping
- Delayed withdrawals
- Internal transfers between hot/cold wallets that obscure the “source of funds”
What analytics needs
- Custody/venue modeling (exchange wallet behavior, clusters)
- Explicit “ledger boundary” concept: the swap is not on-chain
- Careful language: “Likely swapped via exchange,” not “provably swapped”
5. Issuer-coordinated abstraction (e.g. Circle Gateway for USDC)
Happy path
- User expresses intent to move USDC cross-chain
- Issuer coordinates liquidity + settlement
- Destination USDC appears without the user managing bridge mechanics
What you can observe
- Issuer-associated pathways and structured settlement events
- Clearer operational patterns than inventory-based services
Linkage
- Often closer to deterministic than other centralized models because the issuer tends to enforce structured workflows and auditable pathways
Failure modes and edge cases
- Centralization: issuer policy/control changes can affect routes
- Limited scope: asset-specific and chain support constrained
- Liquidity concentration risk
What analytics needs
- Explicit “issuer layer” in the CCS pipeline
- Deterministic mapping when identifiers exist
- Governance/change monitoring (routes can evolve)
6. Intent-aware interoperability (EIL + XLPs)
Happy path
- User submits a cross-chain intent
- XLPs/solvers compete to fulfill it quickly
- Fulfillment happens on destination chain
- Settlement is enforced by Ethereum-secured messaging / proofs
What you can observe
- Structured intent objects (or intent-like metadata)
- Solver fulfillments
- Canonical settlement proofs/messages
Linkage
- Tends toward deterministic if intent identifiers and settlement proofs are first-class primitives
Failure modes and edge cases
- Solver market maturity (liquidity fragmentation early on)
- Monitoring complexity (more moving parts than classic bridges)
- Protocol evolution (standards still changing)
What analytics needs
- First-class representation of intent → fulfillment → settlement
- Deep protocol decoding + message correlation
- Standardized identifiers across legs
{{horizontal-line}}
The 2026 landscape: Swaps didn’t converge — they fragmented
Cross-chain swaps have not converged to a single model.
Instead, we now have a spectrum:
- Protocol-native CCS (intent-aware interoperability layers)
- Issuer-coordinated abstraction (USDC-style pathways)
- DeFi liquidity bridges
- Traditional lock-and-mint bridges
- Centralized instant swap desks
- Fully custodial internal swaps
Each optimizes for a different axis:
- Speed
- Liquidity efficiency
- Decentralization
- Compliance
- Observability
- UX simplicity
And critically: Cross-chain swaps don’t eliminate traceability — they relocate it.
Some systems make intent explicit on-chain. Some hide causality inside inventory systems. Some push the truth into internal ledgers.
In 2026, the right question isn’t “is CCS traceable?” It’s:
Where does this model put the truth, and what does it expose?
{{horizontal-line}}
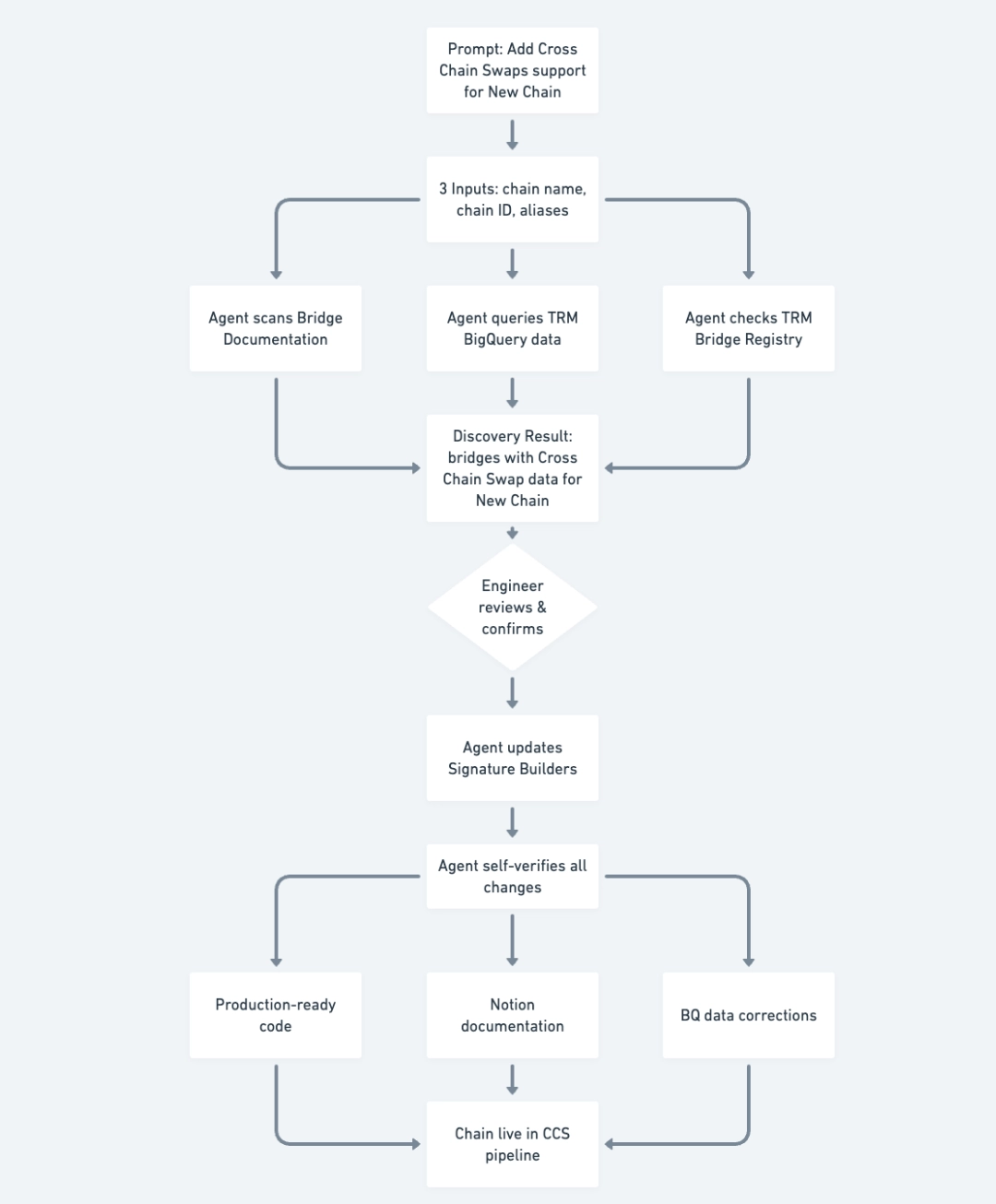
Future of cross-chain swaps at TRM
At TRM, the goal isn’t just “more bridges” — it’s repeatable CCS coverage across every swap model, shipped fast enough to keep up with chain fragmentation. We’ve already pushed in that direction by building Day-0 CCS support workflows that combine on-chain data, public protocol docs, and TRM datasets to stand up new coverage quickly.
What the “future” looks like is basically doing that systematically, model by model:
Traditional bridges (Wormhole / lock-mint systems): Protocol-aware decoding + deterministic linkage primitives
We treat bridge messages and identifiers as first-class linkage keys (message IDs / nonces / sequences) so the system can produce high-confidence source → destination mappings when protocols expose stable identifiers.
Liquidity-based bridges / cross-chain DEXs: Confidence-scored linkage + explainability
These protocols often generate multi-step fills and delayed settlement, so the focus is on (a) extracting the protocol structure and constraints, and (b) grading linkage confidence instead of forcing brittle “always-deterministic” assumptions.
Centralized swap services and custodial ledgers: Observability hooks + probabilistic linkage
Since the “join” often lives inside internal systems, the practical goal is to make these cases tractable for analysts: detect the legs reliably, assign explicit confidence to the inferred linkage, and explain why the system believes two legs belong together.
Intent-aware systems (EIL-style): Canonical intent → fulfillment → settlement primitives
Under the hood, the roadmap is also very concrete infrastructure work: actively decouple cCross-c Chain sSwap computation from batch constraints into a modular architecture designed to (1) cut costs, (2) speed up onboarding, and (3) lay the foundation for real-time/event-driven processing. S
Finally, we’re also grounding speed and correctness in partnerships: Adding coverage is intensive (investigation, test transactiions, heuristics, scraping/ingestion, and deposit ↔ withdrawal linking), and that partner data access can materially reduce development time and improve correctness/completeness.
If CCS modeling is fast to onboard, explicit about confidence, resilient to protocol upgrades, and readable to humans, then CCS stays tractable — even as the ecosystem keeps changing.
{{horizontal-line}}
Conclusion
Cross-chain swaps aren’t a niche mechanic anymore — they’re the default way value moves in crypto. But the big takeaway is that “a CCS” isn’t a single thing you can track with a single rule: every model makes different trade-offs, and those trade-offs determine where the truth of a swap lives. Sometimes the linkage is provable via a shared message ID and on-chain proofs; sometimes it’s constrained but noisy because fulfillment and settlement are separated; and sometimes the causal join disappears into inventory systems and internal ledgers.
Our point of view is that CCS becomes tractable when you treat linkage as a first-class problem: decode protocols when deterministic identifiers exist, assign explicit confidence when they don’t, and represent every swap in a canonical schema that stays stable even as protocols evolve. In other words, the right question isn’t “is CCS traceable?” — it’s “where does this model put the truth, what does it expose, and how clearly can we quantify what we know versus what we’re inferring?” That’s the lens TRM brings to cross-chain swaps: not just broader coverage, but more durable, explainable, confidence-aware truth in a world where value keeps moving across more chains every day.
{{horizontal-line}}
Appendix: Quick checklist for “how traceable is this CCS?”
When evaluating a CCS system, ask:
- Is there a stable identifier connecting source → destination?
- Is intent encoded on-chain, or implied by deposits/withdrawals?
- Is liquidity fronted (fulfillment ≠ settlement)?
- Is the coordinator a protocol or a service with inventory?
- Does the model introduce batching or netting that breaks 1:1 mapping?
- Can you observe settlement/finality, or only fulfillment?
This checklist turns “CCS is hard” into a set of concrete engineering questions.
{{horizontal-line}}
Interested in this kind of work? We’re hiring engineers who like complex distributed systems and correctness problems. Check out our open roles and apply here.






















