THORChain Exploit Drains USD 11M+ Across at Least Nine Chains: What TRM Knows Now

Key takeaways
- An attacker drained more than USD 11 million in assets from THORChain on May 15, 2026, across Bitcoin, Ethereum, Binance Smart Chain (BSC), Base, Avalanche, DOGE, Litecoin, Bitcoin Cash, and XRP
- Cumulative THORChain losses from thefts since 2021, including one targeting its founder, now approach USD 25 million
- TRM is monitoring outflows from the consolidation cluster and will update attribution as the picture develops
What happened
THORChain enables native cross-chain swaps without wrapped assets, making it both useful infrastructure and a recurring target. On May 15, the attacker compromised functions across at least nine supported chains and drained funds simultaneously.
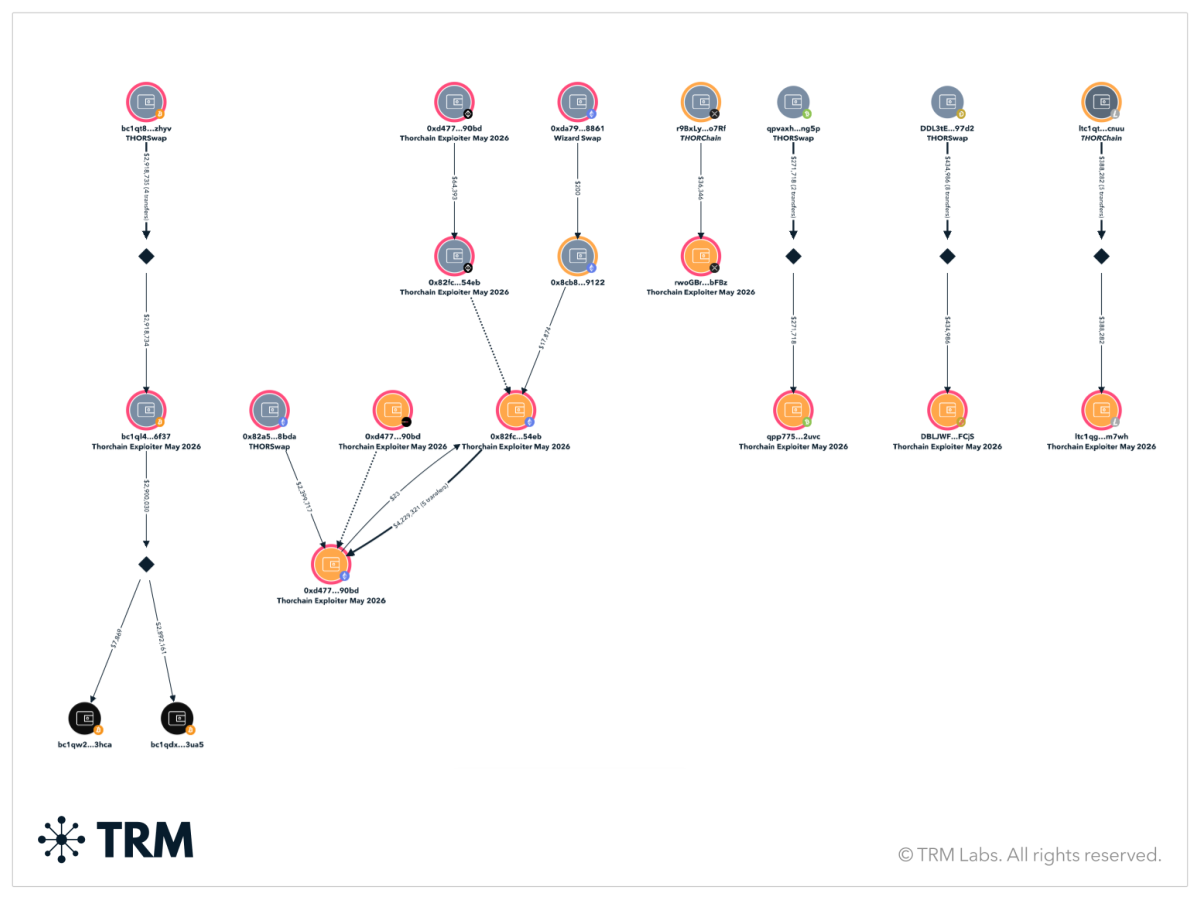
Initial attacker addresses receiving the stolen assets:
- BTC: `bc1ql4u94klk265lnfur2ujk9p6uh52f2a8jhf6f37`
- EVM: `0x82fc0d5150f3548027e971ec04c065f3c93154eb`
- EVM: `0xd477b69551f49c0519f9b18c55030676138890bd`
- BCH: ‘qpp775v2je9texcv54rhd6kl9pfudy2nyyz4df2uvc’
- DOGE: ‘DBLJWFemMHbduKofBRg6TJ9XFAgWdvFCjS’
- LTC: ‘ltc1qg0h4rz5kf27fkr99gamw4heg20rfz5epd7m7wh’
- XRP: ‘rwoGBrYEJ28jhBjchrTyCGXd1Pt4pobFBz’
What TRM has done
TRM investigators tagged the five addresses and traced flows across all four affected chains within hours of the initial drain.
Cross-chain exploits shorten investigative timelines. Funds can move between chains faster than traditional attribution workflows can keep up, which is why THORChain is a recurring target — and why speed matters here. The attacker spread the drain across Bitcoin, Ethereum, BSC, and Base, then pulled the proceeds back into a two-address consolidation cluster.
Why THORChain matters in this case
THORChain has suffered repeated hacks. It was compromised twice in July 2021 in addition to today’s theft. THOR’s founder, JP Thorbjornsen, was also personally targeted in 2025 by probable North Korean hackers. Cumulative losses from these thefts now approach USD 25 million. THORChain has also become the bridge of choice for the laundering of North Korea’s mega-heists, most notably 2025’s USD 1.5 billion hack of Bybit, and most recently, the nearly USD 300 million hack of KelpDAO. THORChain has consistently refused to block illicit activity, framing its stance as supporting free speech and against “censorship.”
At the time of writing, TRM has not attributed the May 15 exploit to any specific actor. The same cross-chain swap mechanics that make THORChain useful for legitimate users also make it a default rail for moving stolen funds across chains, and the protocol's role as both attack surface and laundering venue is now the operational picture compliance teams are working with.
For compliance teams at exchanges, that means any deposit pathway with THORChain-adjacent counterparty exposure now sits in the path of both these exploit proceeds and a longer pattern of high-volume illicit flows.
What's next
TRM is monitoring outflows from the consolidation cluster and will update attribution as the picture develops. Compliance teams with exposure to the tagged addresses should act within hours, not days — the operational window for freezing or quarantining funds is short.
Frequently asked questions (FAQs)
1. How many chains were affected?
At least nine chains were affected: Bitcoin, Ethereum, Binance Smart Chain (BSC), Base, Avalanche, Dogecoin, Litecoin, Bitcoin Cash, and XRP.
2. Has TRM attributed this exploit to a specific actor?
No. TRM has not attributed the May 15 exploit to a specific actor. Investigation is ongoing, and TRM will update attribution in TRM Forensics as the picture develops.
3. What should compliance teams do if they have exposure to the tagged addresses?
Act within hours, not days. The operational window for freezing or quarantining funds in cross-chain exploits is short — assets can move between chains faster than traditional attribution workflows track. Screen counterparties against the tagged addresses, flag any inbound deposits from those addresses, and monitor TRM Forensics for attribution updates.
4. How does the May 15 theft fit into THORChain’s track record?
THORChain has suffered repeated exploits. The protocol was compromised twice in July 2021, and its founder, JP Thorbjornsen, was personally targeted by probable North Korean hackers in 2025. Cumulative losses from those thefts now approach USD 25 million. THORChain has also served as the primary laundering rail for two of the largest crypto hacks on record — the USD 1.5 billion Bybit hack in February 2025 and the nearly USD 300 million KelpDAO hack in April 2026. The protocol has consistently declined to block illicit activity, framing that stance as opposing censorship.
5. Why does THORChain keep appearing in major crypto thefts?
THORChain enables native cross-chain swaps without wrapped assets, making it both useful infrastructure and a default rail for moving stolen funds. Its mechanics complicate attribution workflows and resist the bridging interdiction that has been used to freeze funds in other exploits. That combination — along with the protocol’s stated refusal to block illicit activity — makes THORChain a recurring presence on both sides of major crypto thefts: as attack surface and as laundering venue.





















