New Disruption Opportunities in the Evolving Ransomware Ecosystem

Key takeaways
- Ransomware activity continued to expand in 2025 even as payments stagnated. Total ransomware-linked volume reached approximately USD 1.3 billion (down from USD 1.9 billion in 2024), while ransom payments held steady at approximately USD 850 million. At the same time, victim postings on leak sites rose by 44%, indicating growing activity alongside declining payment rates. This divide presents four unique opportunities.
- TRM identified 93 new ransomware variants in 2025, a 94% increase from 2024.
- Opportunity 1: Geographic reach is expanding into extraditable jurisdictions. The Ransomware-as-a-Service (RaaS) model has diversified the ransomware ecosystem, dispersing operators across a broader range of countries. TRM's analysis links actors across multiple groups and identifies affiliates in cooperative jurisdictions.
- Opportunity 2: Cyber crime services are a more disruptible layer than ransomware itself. The ecosystem increasingly depends on third-party providers — including initial access brokers, bulletproof hosters, and credential tools — that operate with weaker operational security.
- Opportunity 3: Leaks and physical crimes are generating actionable intelligence. Internal leaks, infrastructure seizures, and crypto-related physical crimes are exposing operator identities and operational details, strengthening attribution and increasing opportunities for real-world enforcement.
- Opportunity 4: Cross-chain laundering is more traceable than actors believe. Ransomware actors are shifting from mixers to cross-chain bridges, perceiving them as offering greater anonymity. However, repeated infrastructure use and consolidation patterns continue to create traceable on-chain footprints, enabling attribution.
{{horizontal-line}}
Record high ransomware fragmentation changes the playing field
Ransomware payments in 2025 totaled approximately USD 850 million—essentially flat from 2024—while the number of victims posted on leak sites grew by 44%. However, when accounting for broader illicit flows into ransomware wallets—including transfers from other ransomware groups and payments from cybercrime services—the total volume received by these actors exceeded USD 1.3 billion. This divergence suggests that, despite an expanded threat landscape driven by lower barriers to entry, victims are increasingly refusing to pay their attackers.
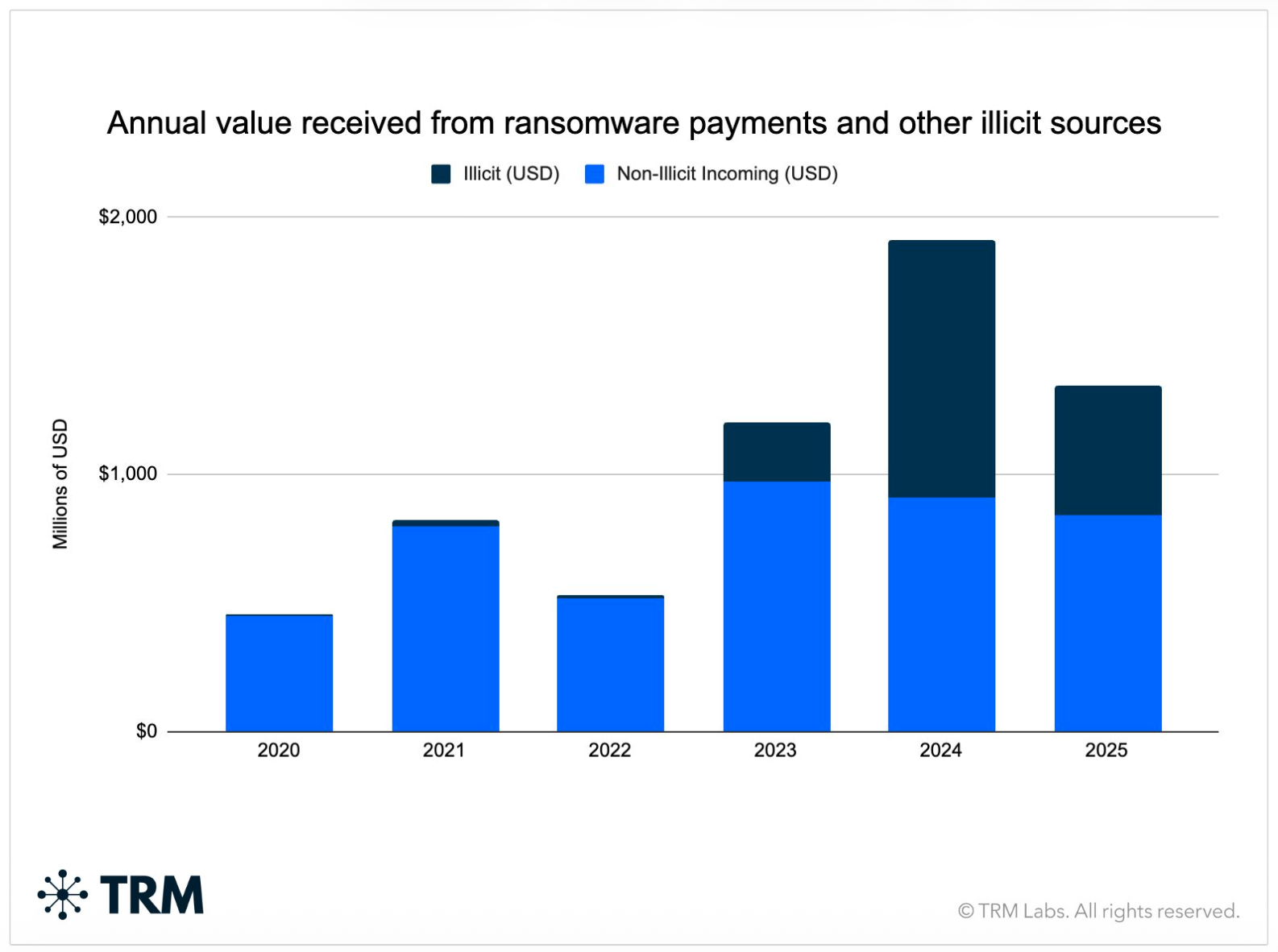
One notable shift in the ransomware ecosystem was the sharp proliferation of new strains: TRM identified 93 new ransomware variants in 2025, a 94% increase from 2024. Despite this surge, payment activity remained concentrated among a relatively small subset of established groups, while the growing long tail of newer or less mature variants generated comparatively minimal revenue.
Payment distribution data reinforces this shift. The number of strains receiving payments in the USD 1,000 to 10,000 range more than doubled from six to 15, and those in the USD 10,000 to 100,000 range rose from 24 to 38. At the same time, activity among mid-sized payment bands (USD 250,000 to 500,000) declined, suggesting a redistribution of payments toward smaller-value extortion events.
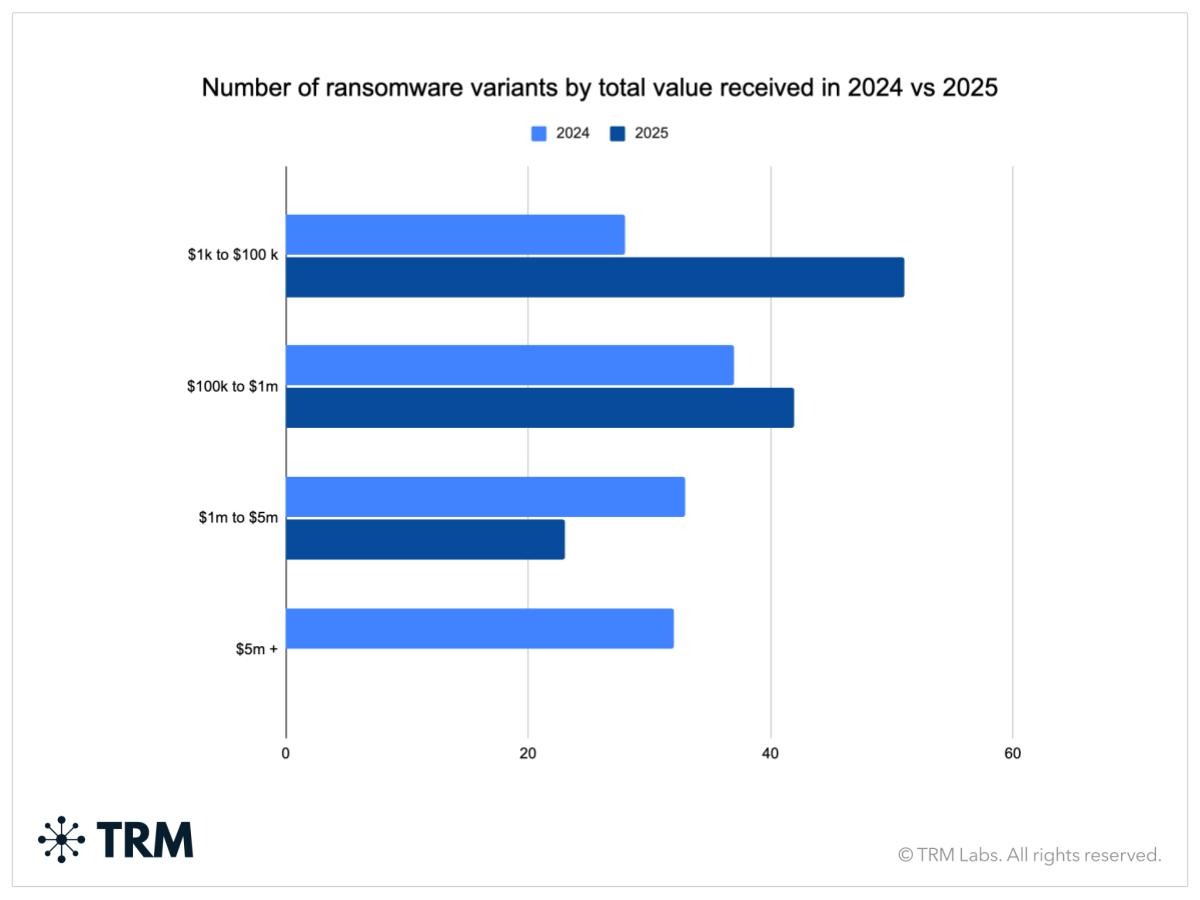
TRM assesses that these patterns likely reflect a combination of factors: the proliferation of new entrants with limited reputation or negotiating power, increased victim resistance to large payouts, and a shift toward opportunistic or lower-complexity attacks that yield smaller but more frequent payments. Rather than consolidating around a few dominant brands, ransomware activity is dispersing across a wider set of actors capturing smaller amounts.
Though many victims are refusing to pay, victimization continues to rise and the ecosystem remains highly regenerative following disruption, as evidenced by the rapid emergence of 93 new variants in 2025 following enforcement actions against major groups. These same dynamics, however, are also creating new opportunities for intervention. Fragmentation has pushed more operators into reachable jurisdictions, increased reliance on service providers with weaker operational security, and generated more intelligence through leaks, seizures, and observable financial behavior.
The result is a ransomware landscape that is harder to suppress through brand-level takedowns alone, but more vulnerable to targeted disruption across the broader supply chain. By examining this divide, TRM Labs identified four specific vectors law enforcement can use against the ransomware supply chain in 2026 and drive greater disruption of threat actors than in previous years.
Opportunity 1: Geographic reach is expanding into extraditable jurisdictions
The RaaS model is predicated on the concept of a core administrative team working to maximize their impact by recruiting a team of affiliates to carry out attacks at scale and provide key services for the group. This model, while lowering the barrier to launching a ransomware operation, often necessitates drawing operators and service providers from across the globe — including many countries in which US and European law enforcement can execute arrests or compel legal processes.
In one investigation that exemplifies this trend, TRM identified a ransomware actor with geolocation data tying them to Ghana, a cooperative jurisdiction. TRM identified five confirmed Bl00dy ransomware victim payment addresses — along with additional addresses used during the laundering phase — using non-VPN IP addresses geolocated to Ghana. Bl00dy, a RaaS operation that emerged in 2022 as a Conti spin-off, has targeted healthcare and education organizations primarily in the United States. The Ghana-based actor's presence in the laundering chain — in a jurisdiction with active law enforcement cooperation — offers a disruption opportunity because the affiliate, mid-tier layer of the ransomware ecosystem is now reachable. On-chain flow analysis combined with geolocation data and leaked identity information creates actionable targeting packages against actors who are both operationally significant and legally accessible.
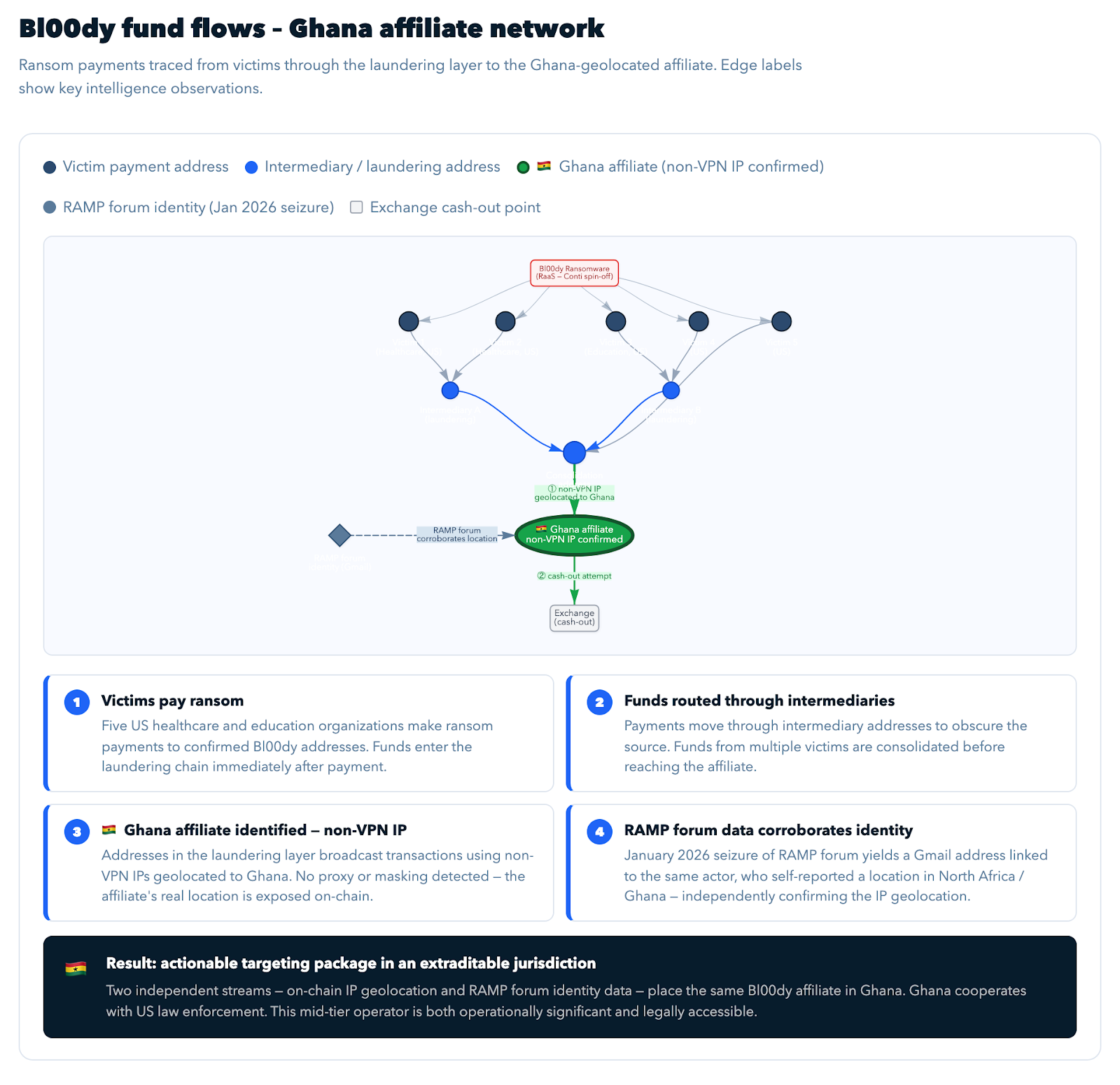
Despite the increased vulnerability of the mid-tier layer, the core administrator layer of the ransomware ecosystem remains concentrated in jurisdictions law enforcement struggles to reach. RaaS is broadening the geographic footprint of middle-level affiliates, but top administrators are still out of reach as they are still in Russia or places US and European law enforcement can't access. However, this mid-tier access still enables investigators to generate leads on the locations of the broader ecosystem, track group behavior to better understand operations, and increase overall chances of seizing victim funds.
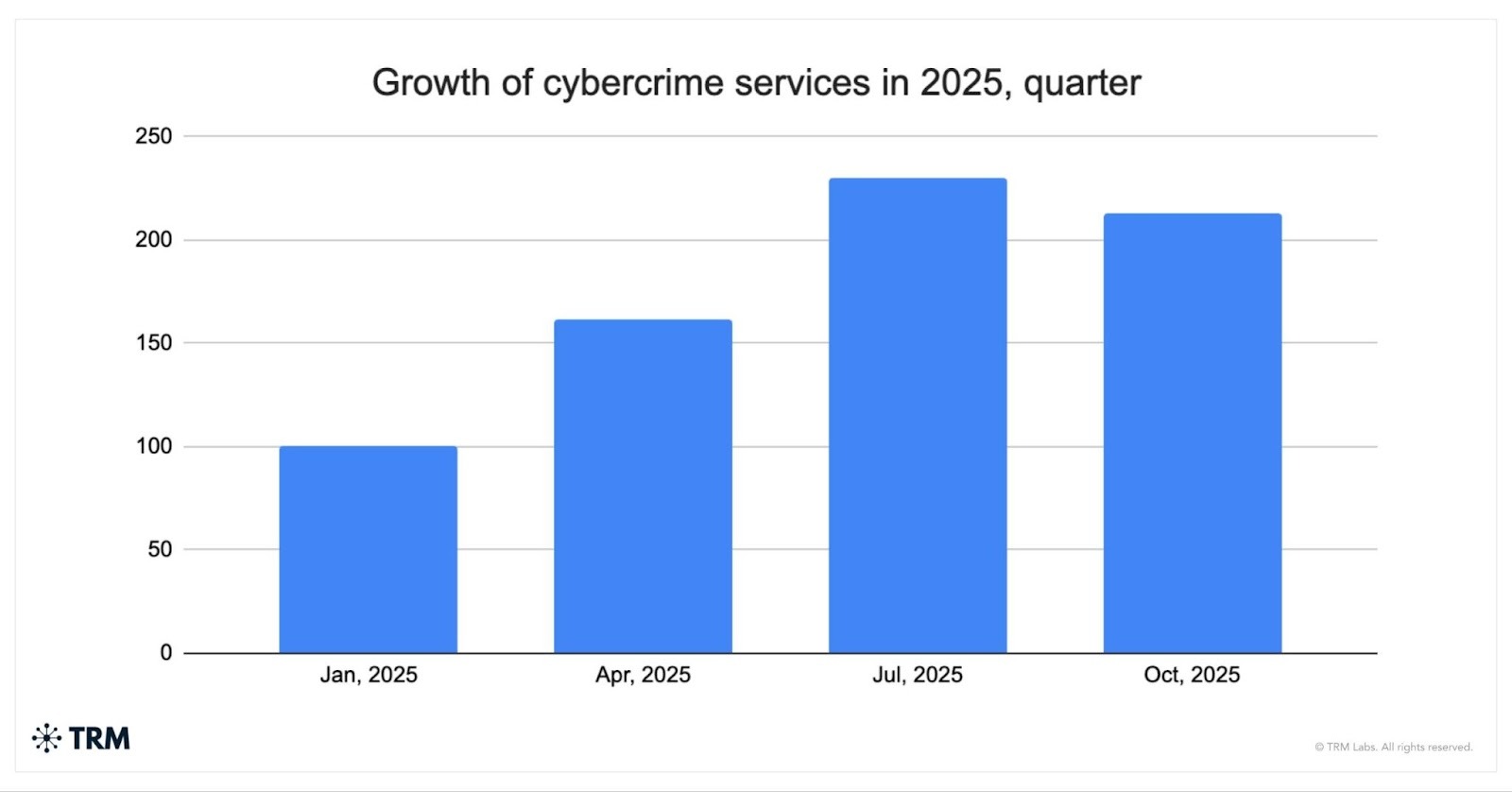
Opportunity 2: cyber crime services are a more disruptible layer than ransomware itself
The cyber crime services underpinning ransomware operations — including initial access brokers (IABs), bulletproof hosters, malware developers, and credential-checking services — expanded throughout 2025. The total amount received by these services more than doubled between Q1 and Q3, followed by a slight retraction in Q4. Generally, these services operate with weaker operational security than the ransomware groups they support. As a result, they present a more accessible point of intervention for law enforcement. Additionally, when these types of services are disrupted, they can impact more ransomware groups that rely on them, amplifying the overall effect of enforcement actions.
IABs advertise access to compromised networks on criminal forums. Their need to be visible to attract buyers creates an identity trail that ransomware operators, who operate more covertly, do not leave.
TRM assesses that many attacks on critical infrastructure begin with initial access brokers on the different cyber crime mediums. IABs are cybercriminals who specialize in leveraging exploits, social engineering, and malware to acquire a foothold on an entity's networks. Particularly reputable IABs will generally have a network of contacts in ransomware groups and sell directly to them.
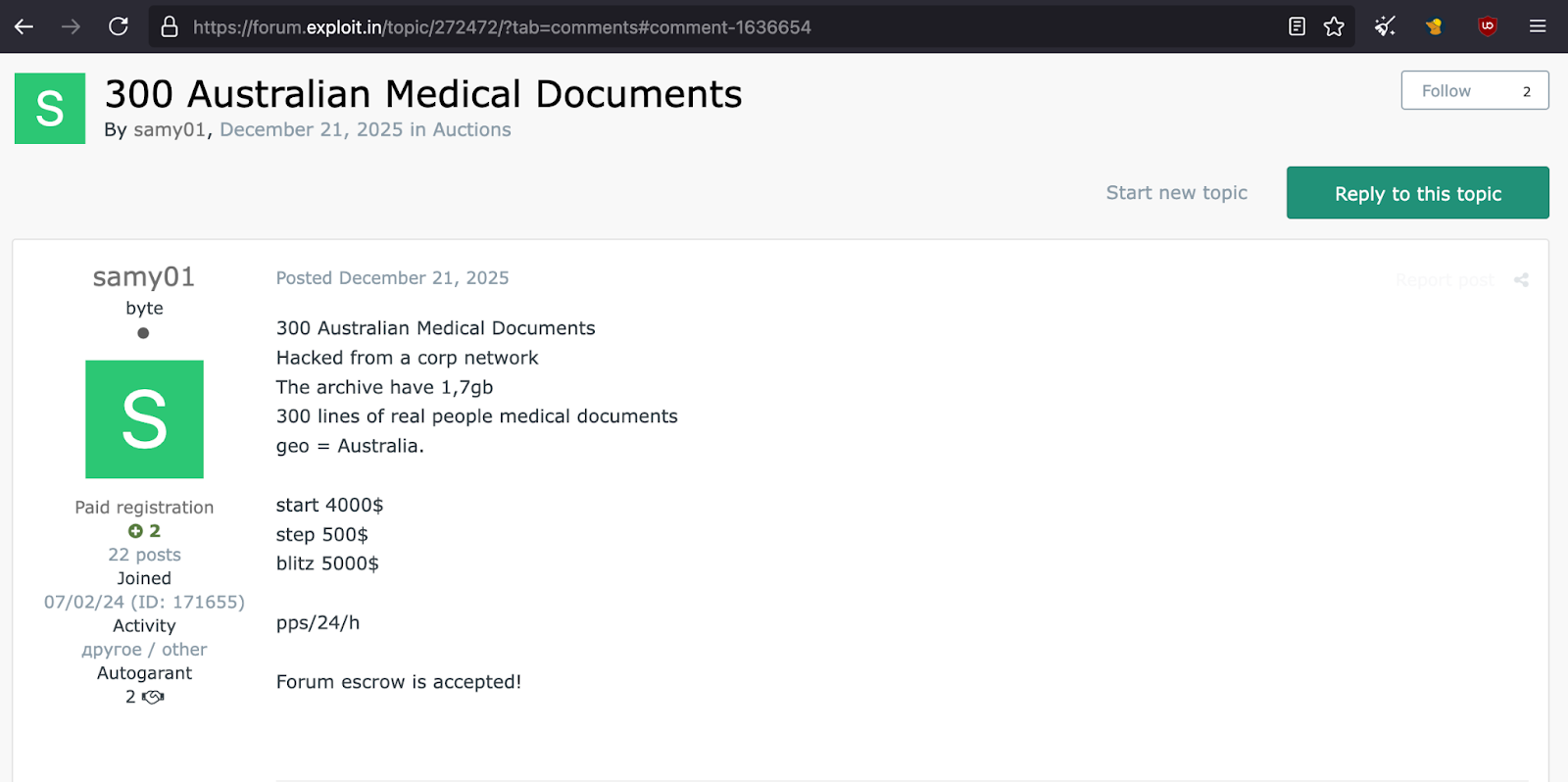
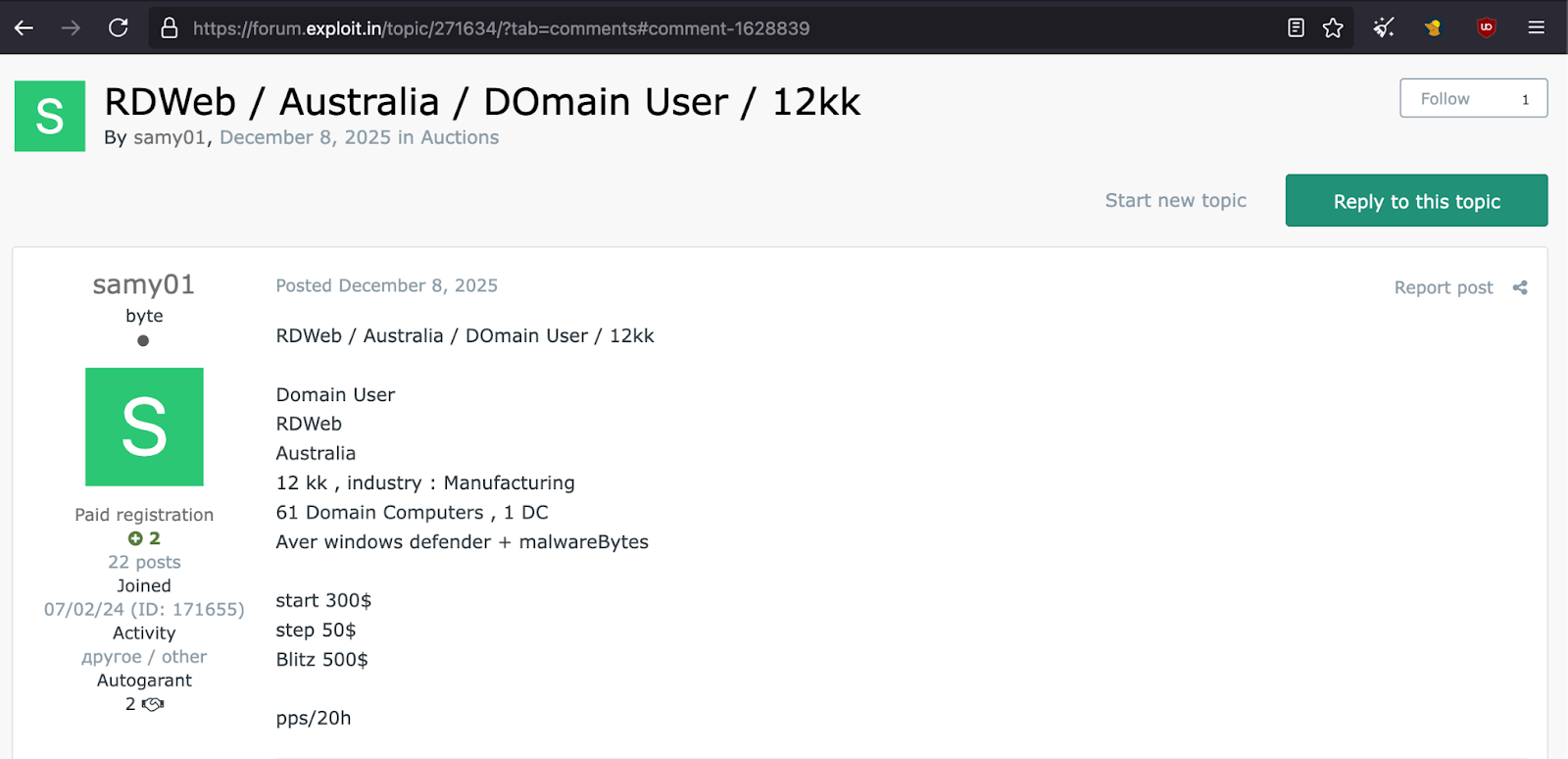
Screenshots of an IAB targeting CNI in Australia. This specific actor serially targeted critical infrastructure in the healthcare sector.
In one investigation targeting the affiliate layer, TRM examined non-VPN IP addresses in Iran, accessing a cluster of almost 200 addresses used to launder funds from victim payments across four ransomware groups: INC, Lynx, Sinobi Group, and info@ranshelp. Using the predictable financial structure of RaaS payout splits — typically 80% to the affiliate and 20% to the admin — TRM distinguished affiliate flows from administrator flows across the payment set. Of 15 victim payments traced, TRM connected nine flows to addresses associated with administrator activity and six to affiliate activity.
This investigation also identified deposits from Sinobi-linked addresses to HashCr4cker, a credential decryption service, and to Bearhost, a bulletproof hosting provider. Targeting the cyber crime services layer disrupts multiple ransomware groups simultaneously rather than one at a time, and IABs and bulletproof hosters can be quantitatively easier targets to disrupt than ransomware groups (i.e. an IAB may be a one-or-two-person operation with poor operational security).
Opportunity 3: Leaks bolster available intelligence, kinetic crimes offer real-world leads
Internal faction leaks, hacktivist intrusions, and server seizures have produced operator-level intelligence that on-chain analysis alone cannot surface. When LockBit and BlackBasta's internal communications leaked, investigators gained access to negotiation transcripts, internal operational discussions, and direct communications between operators and victims. This data ties pseudonymous crypto addresses to operator monikers and monikers to real-world identities. Leaks also create infighting and paranoia inside criminal networks — raising the operational cost of running a ransomware ecosystem, slowing recruitment, and eroding trust in shared infrastructure. Each leak event degrades the targeted group and the confidence of the broader ecosystem.
The Russian Anonymous Marketplace (RAMP) forum seizure in January 2026 yielded registration data, access logs, and infrastructure details suitable for cross-referencing with blockchain attribution. For example, TRM analysts found an email address in the RAMP leaked data where the actor from the Bl00dy group mentioned in Opportunity 1 advertised their location as North Africa.
Additionally, kinetic crypto-related crime — where attackers use force, intimidation, or coercion to compel victims to hand over crypto — is rising, and offers a distinct disruption opportunity due to the physical nature of the activity. TRM's joint white paper with the Metropolitan Police Service identified 17 reported offenses in London over nine months, and kidnapping — which accounted for the majority of cases — is the offense type with the highest arrest rate. Physical crimes require physical presence, leave biometric and video evidence, and actors skip laundering steps, producing cleaner on-chain traces.
Opportunity 4: Cross-chain laundering is more traceable than actors believe
Ransomware actors have shifted away from mixers toward bridges, believing cross-chain movement provides greater obfuscation. On-chain evidence indicates this assumption is increasingly wrong.
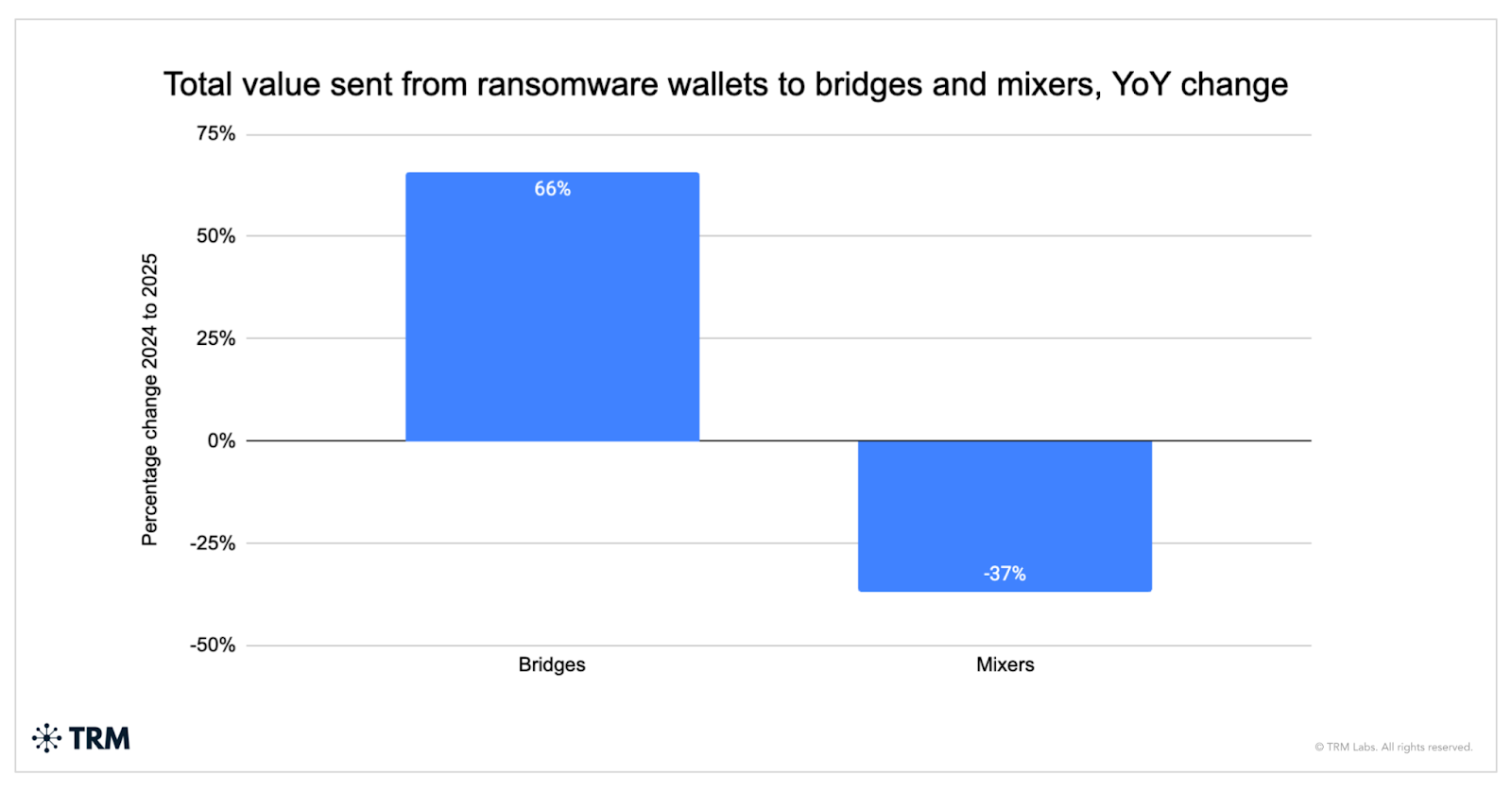
Bridge-related activity from ransomware wallets grew 66% year over year; mixer-related activity declined 37%. Funds routed through bridge services remain highly traceable, particularly when actors reuse infrastructure or consolidate at common cash-out points — patterns that are consistently observed across both group- and affiliate-level laundering operations.
Looking at longstanding ransomware group Akira, TRM tracked four distinct laundering evolutions, several of which use bridges — including WanChain and Defiway — demonstrating that patterns can be identified regardless of the mechanism. Akira received approximately USD 150 million in 2025, and recent deviations show victim funds routed through Chainflip into Tornado Cash, potentially the beginning of a fifth laundering evolution. This rapid identification of new tactics can provide law enforcement with the ability to seize victim funds based on anticipated cash-out points.
What this means for disruption strategy in 2026
The old playbook — take down the brand, seize the infrastructure — can be outdated when deployed against a 161-variant ecosystem where displaced affiliates reconstitute in weeks. Four tactical windows are open in 2026 that did not exist at this scale before: more operators in reachable jurisdictions, a weaker-opsec services layer, unprecedented intelligence yield from leaks and seizures, and a laundering layer that is more traceable than commonly known.
Tools like TRM enable identity-level attribution across multiple ransomware groups simultaneously, from IPs to wallets to operators. If the opportunities identified above are combined with tools like TRM and timely, strategic targeting from investigators and prosecutors, ransomware groups will face one of their toughest challenges yet.
{{horizontal-line}}
Frequently asked questions (FAQs)
1. Why did ransomware payments stagnate in 2025 even as attacks increased?
More victims are refusing to pay. Victim postings on leak sites rose 44% in 2025, but total ransom payments held steady at approximately USD 850 million. This reflects both greater victim resistance to large payouts and a proliferation of smaller, opportunistic attacks that yield lower payments.
2. What is the Ransomware-as-a-Service model and why does it matter for disruption?
Ransomware-as-a-Service (RaaS) allows criminal operators to license ransomware tools to affiliates, who conduct attacks in exchange for a share of the proceeds — typically 80% to the affiliate and 20% to the administrator. This model has lowered barriers to entry and dispersed ransomware activity across a wider geographic and operational footprint, creating both new disruption challenges and new targeting opportunities.
3. How are cybercrime service providers a more accessible disruption target than ransomware groups themselves?
Ransomware operations depend on a layer of third-party services — initial access brokers, bulletproof hosters, and credential-checking tools — that operate with weaker operational security. Many of these providers are small operations that must remain visible on criminal forums to attract buyers, creating identity trails that ransomware operators, who operate more covertly, do not leave. Targeting this layer can degrade multiple ransomware groups simultaneously.
4. Why are cross-chain bridges less anonymous than ransomware actors believe?
Ransomware actors have shifted from mixers to cross-chain bridges (+66% year over year), assuming they provide greater obfuscation. However, actors frequently reuse infrastructure and consolidate at common cash-out points, creating consistent on-chain fingerprints. TRM's tracking of Akira across four distinct laundering evolutions shows that even evolving methods produce identifiable patterns.
5. What role do leaks and physical crimes play in ransomware investigations?
Internal leaks — such as those from LockBit and BlackBasta — expose negotiation transcripts, operator monikers, and real-world identities that on-chain analysis alone cannot surface. Forum seizures such as RAMP yield registration data and access logs that can be cross-referenced with blockchain attribution. Kinetic crypto-related crimes (where attackers use force or coercion to obtain crypto) also offer unique leads: physical presence requirements, biometric and video evidence, and cleaner on-chain traces due to skipped laundering steps.
6. What limits law enforcement's ability to reach the top tier of ransomware operators?
Core RaaS administrators remain concentrated in jurisdictions — primarily Russia — where US and European law enforcement cannot execute arrests or compel legal processes. However, the mid-tier affiliate layer is increasingly operating in cooperative jurisdictions, creating opportunities for targeted action that can also generate intelligence on broader group operations and increase the chances of seizing victim funds.





















