DOJ Seizes USD 61 Million Tied to Pig Butchering Scam in North Carolina

Key takeaways
- DOJ seized USD 61 million tied to pig butchering scams. US authorities seized more than USD 61 million in USDT linked to cryptocurrency investment fraud schemes known as pig butchering scams.
- Pig butchering scams drive large-scale crypto fraud. These schemes use long-term social engineering and fake crypto trading platforms to extract large sums from victims.
- Blockchain tracing enabled investigators to follow stolen funds. Despite laundering attempts across wallets and blockchains, investigators traced transactions and identified consolidation wallets holding victim funds.
- Rapid reporting helps recover stolen cryptocurrency.Early victim reporting and coordination between law enforcement and digital asset companies increase the chances of tracing and seizing illicit funds.
{{horizontal-line}}
DOJ seizes USD 61 million in cryptocurrency linked to pig butchering schemes
Last week, the US Attorney’s Office for the Eastern District of North Carolina announced the seizure of more than USD 61 million worth of USDT tied to cryptocurrency investment fraud schemes commonly known as pig butchering scams. The seizure reflects a coordinated investigation led by Homeland Security Investigations (HSI) Raleigh, with support from HSI’s International Operations Division, and demonstrates the increasing sophistication of blockchain tracing and asset forfeiture efforts in large-scale crypto-enabled fraud cases.
According to court filings, the seized funds were traced to cryptocurrency addresses associated with laundering proceeds derived from victims of investment fraud schemes. The investigation began with a victim complaint submitted through the HSI Tip Line and ultimately led to the identification of commingled wallets containing substantial balances of victim funds that were subject to seizure and forfeiture.
TRM is proud to have supported HSI in this investigation.
Anatomy of a pig butchering scheme
Pig butchering schemes are structured, long-duration social engineering fraud operations designed to maximize financial extraction from victims over time. Criminal actors typically establish trust with victims under the pretense of a romantic relationship or close personal connection. Once rapport is secured, the scammer introduces what appears to be a lucrative cryptocurrency investment opportunity, often claiming access to proprietary trading strategies or exclusive market insight.
Victims are directed to fraudulent cryptocurrency trading platforms that closely mimic legitimate exchanges in branding, functionality, and user interface. These platforms display fabricated account balances and trading gains, creating the illusion of sustained profitability. In many cases, victims are permitted to withdraw small amounts early in the process to reinforce credibility and build confidence. As investment amounts increase, victims are confronted with fabricated requirements such as “tax payments,” “compliance fees,” or “liquidity verification deposits” before withdrawals can be processed. At that stage, the funds are no longer recoverable through the fraudulent platform because they have already been transferred to wallets controlled by the perpetrators.
The operational structure of these schemes is engineered for repeatability. Engagement teams handle victim communication. Technical teams manage domain infrastructure and platform replication. Financial managers oversee wallet routing and laundering pathways. The objective is not a single fraudulent transaction but a scalable, industrialized extraction model.
Tracing the flow of funds
Once victims transferred funds to cryptocurrency wallets under the scammers’ control, those funds were rapidly routed through multiple intermediary addresses. This layering process is intended to obscure the source, nature, and ownership of the stolen assets. In this case, investigators observed victim funds being commingled with proceeds from other victims across jurisdictions and blockchains.
HSI agents and analysts traced the victim’s funds across a series of wallet hops, identifying transaction patterns consistent with coordinated laundering activity. Even where funds were mixed with other balances, blockchain analytics enabled investigators to cluster addresses based on behavioral indicators and common control characteristics. Through graph analysis, transaction timing review, and exposure mapping, investigators were able to follow the movement of funds into consolidation addresses that retained substantial residual balances.
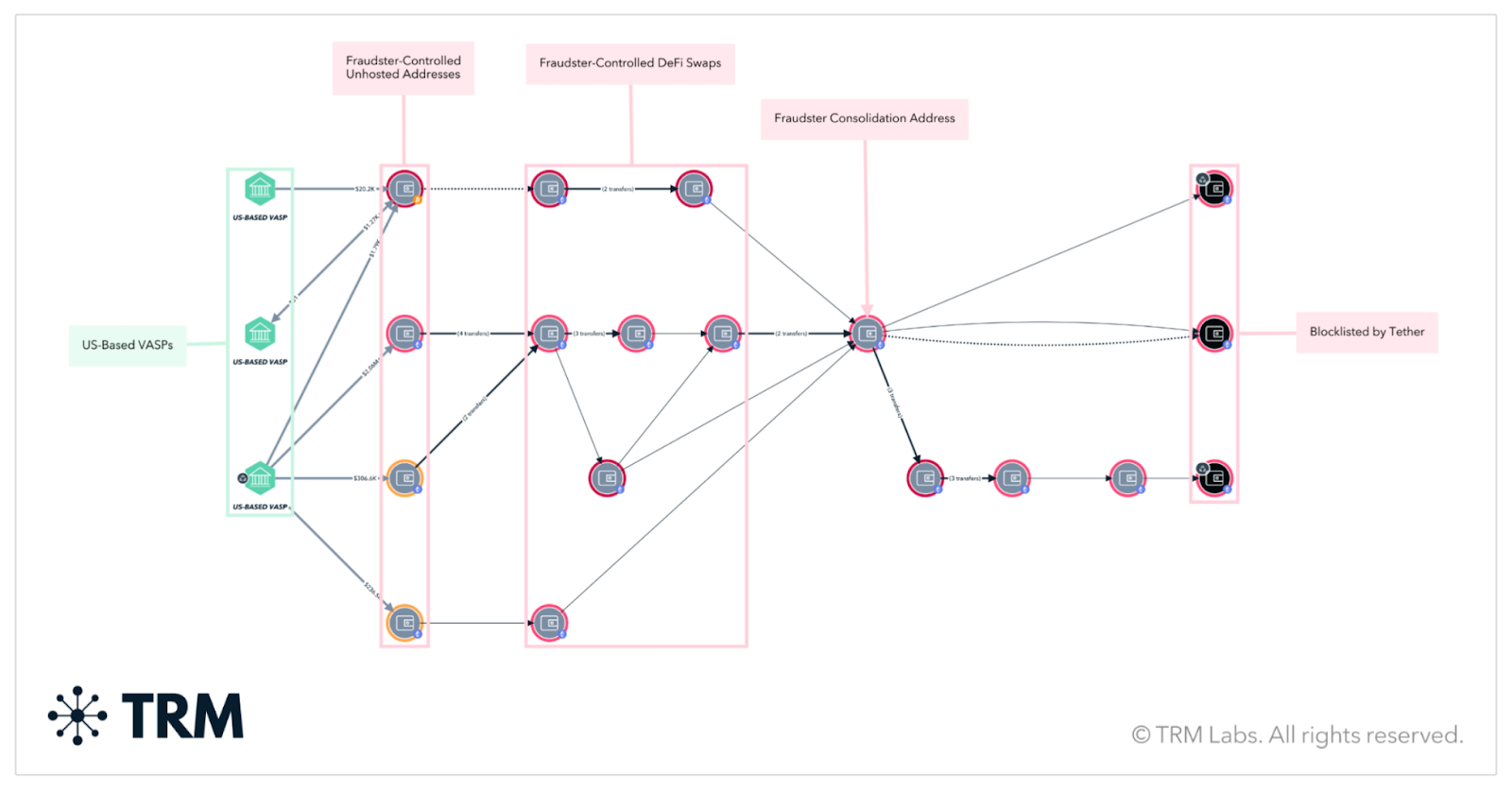
As shown in TRM, HSI investigators traced victim funds from exchanges, through decentralized finance and swapping services, and into commingled consolidation addresses where funds were finally seized
Despite attempts to fragment and obscure the transaction trail, public blockchain ledgers provided an immutable record of each transfer. Investigators reconstructed the flow of funds from the originating victim transaction through intermediary wallets and into addresses where significant funds remained accessible. Those addresses became the basis for seizure and forfeiture action.
The investigation involved tracing funds across multiple blockchain environments and through services frequently used to facilitate obfuscation, including swapping mechanisms and cross-chain transfers. The ability to correlate transaction activity across chains and identify convergence points was central to the seizure.
The role of public-private collaboration
The Department of Justice and HSI acknowledged USDT for its assistance in transferring the seized assets. Cooperation from digital asset issuers and service providers is often essential in asset restraint efforts, particularly when funds remain within environments where freezing or transfer support is technically possible.
Cases of this scale underscore the importance of rapid reporting and real-time collaboration. Pig butchering schemes are intentionally designed to move funds quickly, often within twenty-four to forty-eight hours of receipt. Early victim reporting, structured intake of wallet identifiers and transaction hashes, and immediate analytical review can materially increase the likelihood that funds are identified before full dissipation.
Broader context: The scale of crypto-enabled fraud
The USD 61 million seizure occurs against a backdrop of sustained global fraud activity. According to TRM’s 2026 Crypto Crime Report, USD 35 billion was sent to fraud schemes in 2025. Pig butchering schemes account for a substantial portion of those inflows and represent one of the most financially devastating fraud typologies observed across public blockchains.
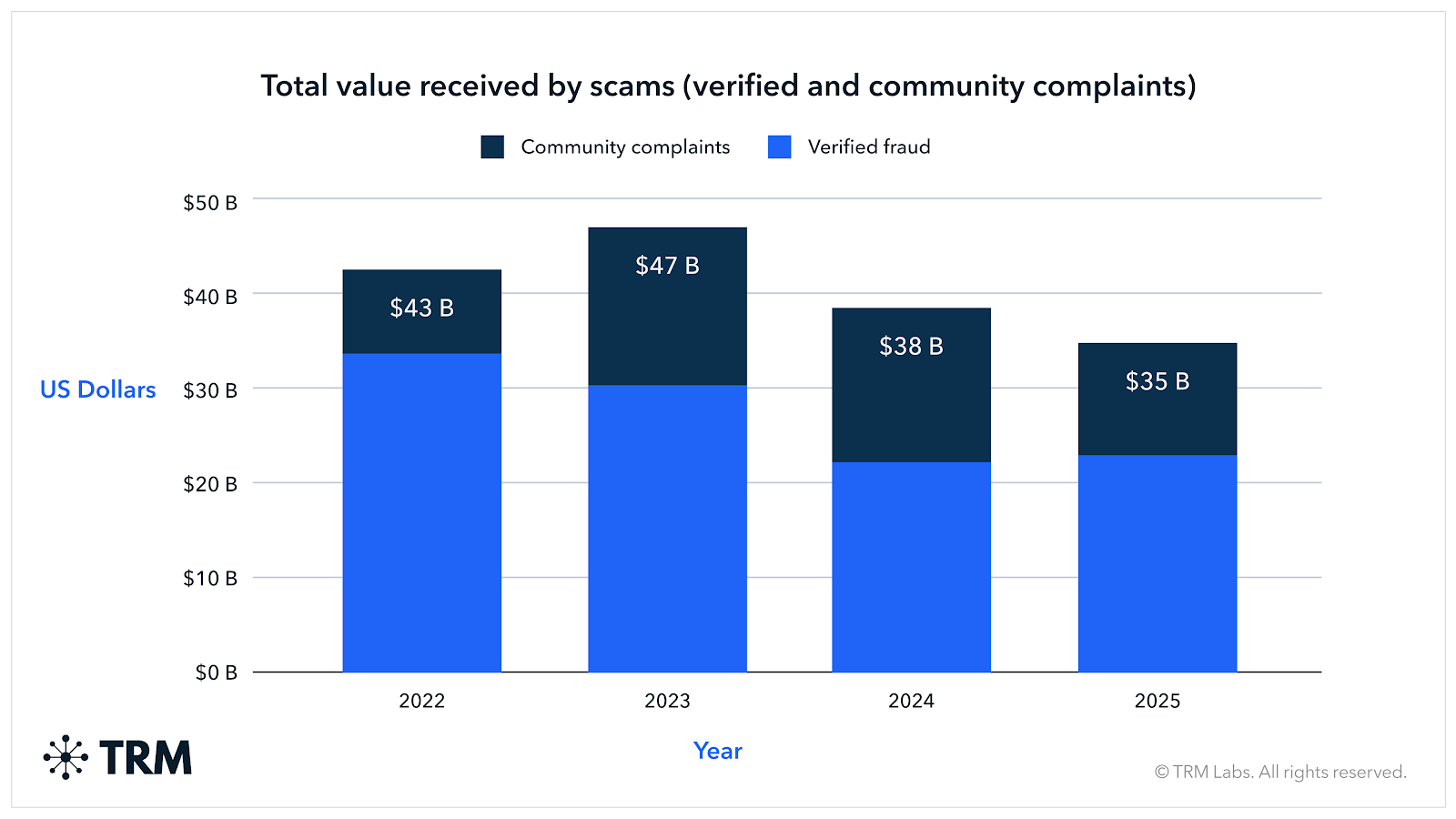
The above figures reflect verified fraud activity from TRM Labs and Beacon Network, as well as alleged fraud activity sourced from Chainabuse, a victim reporting platform operated by TRM
These schemes are global in infrastructure but deeply personal in impact. Victims frequently lose retirement savings, business capital, and life savings accumulated over decades. The psychological harm associated with long-term grooming and betrayal compounds the financial damage.
Operational significance
The Eastern District of North Carolina seizure demonstrates several critical operational realities. First, blockchain transparency remains a structural advantage for investigators. While criminals can layer transactions and commingle funds, they cannot erase transaction history from a public ledger. Second, sophisticated tracing across multiple wallets and blockchains can identify consolidation nodes even in complex laundering structures. Third, asset recovery is possible when investigative tempo matches the speed of fund movement.
The seizure of over USD 61 million in USDT reflects the combined impact of victim reporting, advanced blockchain analytics, coordinated law enforcement action, and cooperation from digital asset ecosystem participants. It also reinforces a central principle of modern financial crime enforcement: even in an environment characterized by speed and technological adaptation, illicit value transfers leave a traceable record.
As crypto-enabled fraud continues to evolve, cases like this demonstrate that with the right tools, training, and coordination, law enforcement agencies can trace, seize, and disrupt large-scale criminal proceeds and work toward returning funds to victims.
{{horizontal-line}}
Frequently asked questions (FAQs)
1. What is a pig butchering scam in cryptocurrency?
A pig butchering scam is a type of cryptocurrency investment fraud where scammers build trust with victims over time — often through social media or messaging apps — before directing them to fake crypto trading platforms that display fabricated profits.
2. How did US authorities seize USD 61 million in cryptocurrency?
Investigators traced stolen funds on public blockchains by analyzing wallet activity and transaction patterns. This allowed law enforcement to identify consolidation wallets holding victim funds and pursue seizure and forfeiture actions.
3. Can stolen cryptocurrency be recovered from scams?
In some cases, yes. Cryptocurrency transactions are recorded on public blockchains, which allows investigators to trace funds. If law enforcement identifies wallets containing stolen assets before they are fully dissipated, those funds may be seized and returned to victims through forfeiture proceedings.
4. Why are cryptocurrency transactions traceable?
Most cryptocurrencies operate on public blockchains that permanently record every transaction. Even when criminals move funds through multiple wallets, exchanges, or chains, investigators can analyze the transaction history to reconstruct the flow of funds.
5. How common are crypto investment scams like pig butchering?
Crypto investment scams are one of the largest sources of cryptocurrency fraud globally. According to TRM’s 2026 Crypto Crime Report, approximately USD 35 billion was sent to fraud schemes in 2025, with pig butchering scams accounting for a significant share.





















